Device Code Phishing, iOS 18 Relief, Global Fraud Disrupted

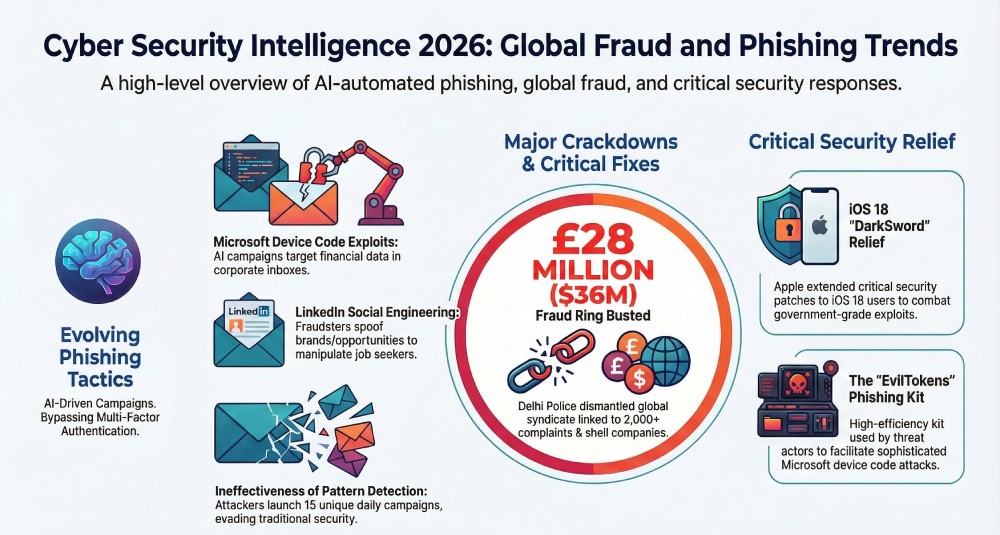
Here are the top cyber incidents from recent times that every cyber enthusiast must be aware of. Hundreds of organizations are getting targeted by Microsoft device code phishing tactics. In a completely unexpected move, Apple has patched the vulnerability against DarkSword in devices with iOS 18. Indian cybersecurity authorities have cracked down on a global cyber fraud ring worth $36 million. Meanwhile, a new phishing campaign is successfully abusing LinkedIn profiles to gain access to login credentials.
Microsoft device code phishing attack exploits organizations to extract crucial financial data!
A new phishing campaign is doing the rounds that involves Microsoft device code and AI automation to successfully break into the email inboxes of corporate employees. Tanmay Ganacharya, the VP of security research at Microsoft, states that around 10 to 15 unique campaigns are being launched daily, and this has been happening since March 15, 2026. The threat actors are tactfully leveraging each campaign to target hundreds of organizations. Because of this tactic, pattern-based detection is proving to be inefficient in this case.

These phishing attacks are designed to target multiple organizations across different global sectors and niches. The finance sector specifically is the worst hit.
There’s yet no clarity around which specific threat group is carrying out this campaign. However, the pattern and tactics hint at EvilTokens, a high-efficiency Microsoft device code phishing kit.
It gained popularity around the middle of February and is used to bypass Multi-Factor Authentication (MFA) systems.
Microsoft recommends blocking device code flow wherever it deems possible. Conducting regular employee training so that they can spot phishing techniques can also be a significant step towards preventing Microsoft device code phishing attacks.
Great relief for iOS 18 users!
For users who are not willing to, or unable to, update their iPhones to iOS 26, there’s some good news from Apple. The tech giant has finally patched the vulnerabilities for each and every customer, even those who are still using the iOS 18 version.

In 2025, too, something similar happened when security researchers discovered Coruna, a government-grade exploit kit. Apple patched all 23 associated vulnerabilities for versions 13 to 17.2.1.
Earlier, those users who were reluctant to upgrade to iOS 26 weren’t offered any security patches by Apple.
But this time, it is about DarkSword, and Apple decided not to take it lightly. Hence, it extended the security fix to every iOS 18 enthusiast.
Cybersecurity experts believe that if Apple is taking DarkSword and Coruna so seriously, then users, too, should understand the gravity of the situation and be vigilant.
A global cyber fraud syndicate worth $36 million was disrupted in Delhi, India!
A major global cyber fraud ring has been busted by the Delhi Police. The same syndicate is involved in cyber scams worth $36 million. A whopping 2000+ complaints have been registered against the same group of threat actors. Authorities managed to crack down on the group and arrest the mastermind alongside 10 others from the same syndicate.
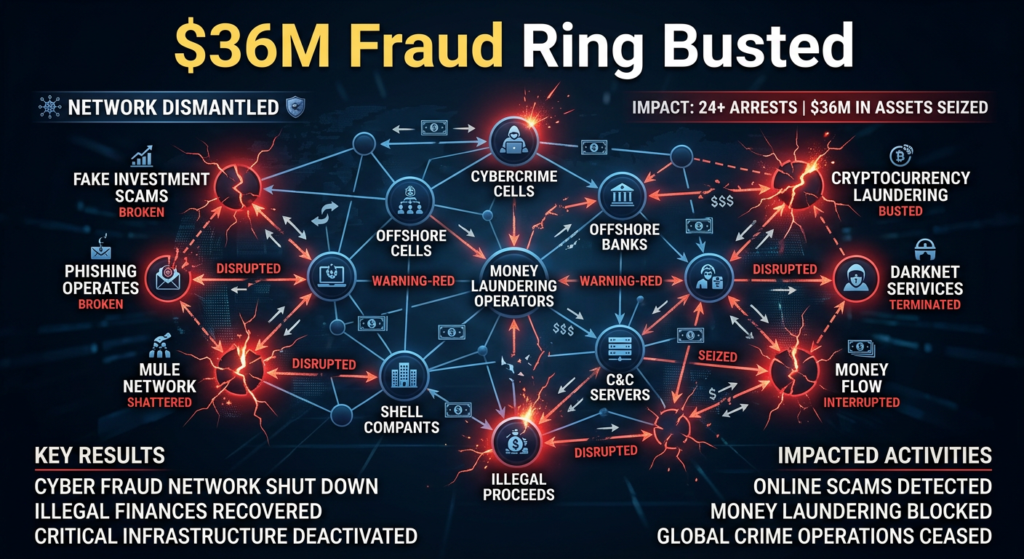
The Delhi authorities discovered this highly organized network that operated across multiple states and had direct connections to international cyber fraud.
The syndicate, headed by Karan Kajaria, used to create false investment platforms as well as messaging platforms to attract their targets. Mule bank accounts were used actively. In order to capture OTPs and other sensitive banking data, the group used malicious applications.
To keep the money trails hidden, the threat actors used to route the collected funds through an intricate web of bank accounts and shell companies.
How to not get duped while using LinkedIn!
LinkedIn is increasingly becoming a popular hunting ground for threat actors. A new phishing campaign is doing the rounds where threat actors have been targeting naive LinkedIn users through LinkedIn notifications.
These threat attacks are often designed as job opportunities. The cybercrooks abuse the desperation and curiosity of job seekers. The hackers are smart enough to use emotional triggers so that the recipients ignore caution and click on the malicious links unsuspectingly.
Phishing messages often pretend to come from reputable companies and influential decision-makers. They carry the right logos, branding assets, and formatting to appear more credible.
Cybersecurity experts have advised LinkedIn users to be aware of unexpected notifications. One must always verify the sender’s authenticity before clicking any link. Automated threat detection and human intelligence have to work together to identify and neutralize such threats in real time.Cybersecurity relies on protocols like DMARC, DKIM, and SPF to authenticate emails, prevent spoofing, and protect domains from phishing attacks.
An upgraded antivirus software and a strong firewall can also prove to be quite handy against such social media-based phishing attacks.