Kratos Targets Outpost24, Intuitive Data Breached, Starbucks Staff Exposed

Phishing attacks dominated last week’s cyberincidents. Outpost24, a security firm, fell prey to a phishing attack. Intuitive’s company data was breached because of a sophisticated phishing attack. A whopping 900 Starbucks employees are now prone to threat attacks after phishing actors breached the internal employee portal.
Meanwhile, a new phishing campaign has been hijacking legitimate websites to target Microsoft Teams users by evading detection systems.
Outpost24 executive targeted with the help of Kratos!

Outpost24 is a Swedish exposure management and identity security firm. Threat actors used Kratos, a popular Phishing-as-a-Service kit, to target Outpost24. The attack was designed in a seven-step chain and comprised a highly intricate, layered infrastructure. Plus, they had genuine services that helped in evading detection and fooling the recipients.
Outpost24 received the phishing message that successfully impersonated the renowned brand JP Morgan. The malicious message looked like a part of an already existing email thread. The message asked the recipient to go through a specific document and then sign it. All the steps were taken carefully to earn the trust of the victim.
The threat actors managed to pass DMARC authentication by using two DomainKeys Identified Mail signatures.
The malicious message consisted of a “review document” link. The same link conveniently passed Cisco’s Secure Email Gateway validation. All these further added to the credibility of the message.
On clicking the link, the victim would be redirected to Nylas, the genuine email API platform. Furthermore, the victim was redirected to a legitimate, India-based development company domain, and then to a 2017-registered domain owned by a Chinese entity.
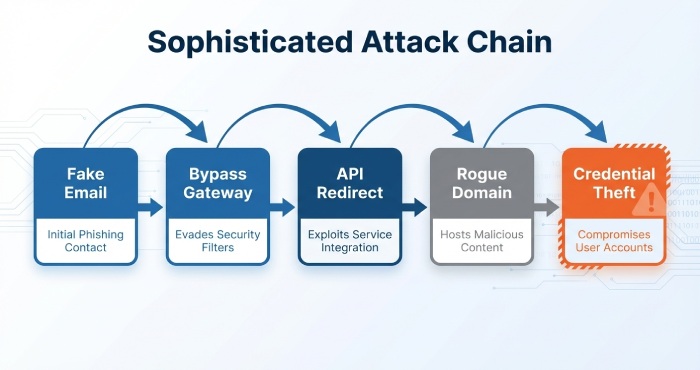
After multiple redirects, the victim landed on a credible-looking phishing page designed for extracting Microsoft 365 credentials.
An Outpost24 spokesperson has confirmed that a C-level executive fell for this sophisticated phishing attack.
Biotech brand, Intuitive’s customer and employee data compromised!
Intuitive, the surgical robotics firm, got targeted by a group of phishing actors. As a result of the cyberattack, the firm’s employee and customer data were compromised.
The cybercrooks managed to gain access to the login credentials of Intuitive’s employees. That’s how they broke into the internal administrative network and finally accessed the data. Intuitive has issued an online statement, shedding light on the data compromised. It includes corporate records, employee records, as well as customer contact and business details.
As soon as the incident came to light, Intuitive deployed its incident response protocols and managed to secure all the applications affected in the phishing attack. An investigation is underway, and experts are also reviewing security protocols. Employees are being trained in online security and risk management.
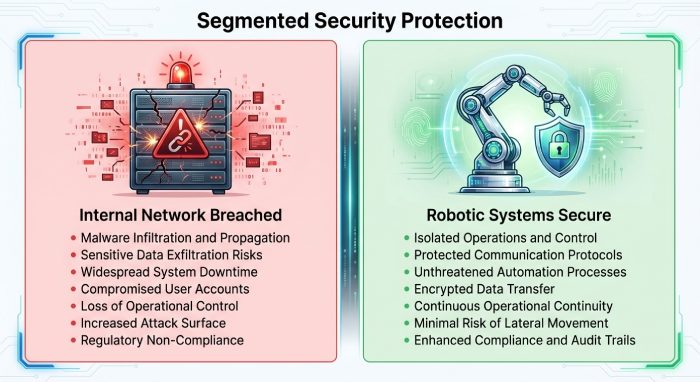
Intuitive believes that the cyberattack could not affect its customer-centric operations.
Since all their robotic systems are equipped with their own security protocols, they can operate separately and independently. That’s why the attack on the internal business network could not disrupt the operations of the robotic system platforms.
Starbucks employee portal targeted, 900 employees stand exposed!

Threat actors managed to break into the Starbucks Partner Central accounts system. This is a SaaS platform used by Starbucks employees to manage all the employment details, such as payroll, leaves, benefits, and so on. Starbucks became aware of suspicious activities back on February 6, 2026. However, after a detailed investigation, Starbucks realized that the breach had happened somewhere between January 19 and February 11.
The phishing actors managed to access employee login credentials by directing the Starbucks employees to malicious websites. These websites are carefully structured to mimic the genuine Partner Central login page. By using this phishing strategy, threat actors were able to authenticate into real accounts without having to directly penetrate the core infrastructure of Starbucks.
The coffee giant has already notified law enforcement agencies. They have also bolstered the security controls on Partner Central. Starbucks has stated that this data breach won’t affect customers in any way.
Legitimate domains misused to target Microsoft Teams users
A new phishing campaign is doing the rounds that abuses legitimate domains to harvest the credentials of Microsoft Teams users.
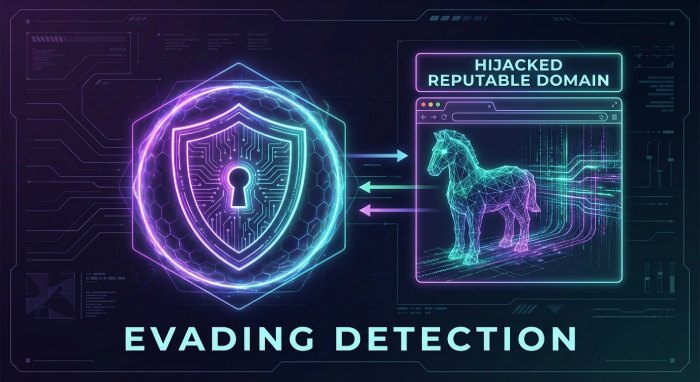
A group of security researchers from a reputed security firm has discovered a massive phishing operation that has been misusing WordPress websites to create credential-harvesting pages.
They embed malicious content within the content of these credible and reputable domains. This significantly minimizes the risk of being detected by any cybersecurity tools and spam filters.
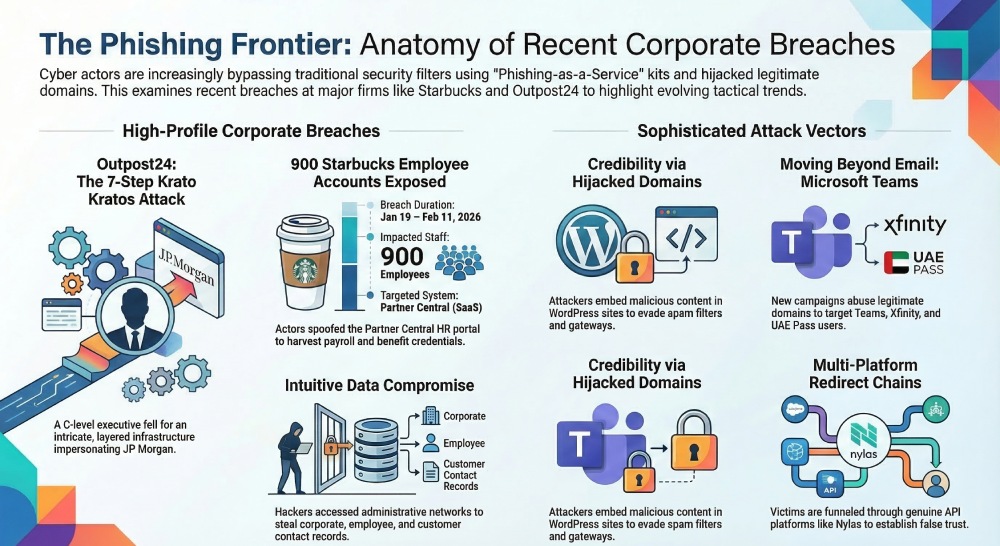
Primarily, the cybercrooks target Microsoft Teams users. But lately, they have also started targeting UAE Pass and Xfinity accounts.
The reason behind hijacking already existing, trustworthy domains is to boost the success rate of the phishing campaign. The malicious URLs look genuine to the victims and increase the likelihood of the target falling for the cyberattack.







