Cybercriminals Target X, Nigeria Fights Cyberattacks, Threat Actors Attack

Quick Answer
_According to the FBI's 2022 Internet Crime Report (IC3), 300,497 US-based victims reported phishing incidents in a single year, and Business Email Compromise (BEC) caused more than $2.7 billion in direct losses. DMARC Report Cybercriminals Target X, Nigeria Fights Cyberattacks, Threat Actors Attack
Related: Free DMARC Checker ·How to Create an SPF Record ·SPF Record Format


From a product strategy perspective, DMARC reporting is evolving from a security tool to a business intelligence platform, says Brad Slavin, General Manager of DuoCircle. The data in aggregate reports tells you not just who’s spoofing you, but who’s sending legitimate email on your behalf - and whether they’re doing it correctly.
_According to the FBI’s 2022 Internet Crime Report (IC3), 300,497 US-based victims reported phishing incidents in a single year, and Business Email Compromise (BEC) caused more than $2.7 billion in direct losses. DMARC Report
Cybercriminals Target X, Nigeria Fights Cyberattacks, Threat Actors Attack
<button title="Play" aria-label="Play Episode" aria-pressed="false" class="play-btn">
Play Episode
</button>
<button title="Pause" aria-label="Pause Episode" aria-pressed="false" class="pause-btn hide">
Pause Episode
</button>
<audio preload="none" class="clip clip-21129">
<source src="https://media.mailhop.org/dmarcreport/images/2025/02/Cybercriminals-Target-X-Nigeria-Fights-Cyberattacks-Threat-Actors-Attack.mp3">
</audio>
<button class="player-btn player-btn__volume" title="Mute/Unmute">
Mute/Unmute Episode
</button>
<button data-skip="-10" class="player-btn player-btn__rwd" title="Rewind 10 seconds">
Rewind 10 Seconds
</button>
<button data-speed="1" class="player-btn player-btn__speed" title="Playback Speed" aria-label="Playback Speed">1x</button>
<button data-skip="30" class="player-btn player-btn__fwd" title="Fast Forward 30 seconds">
Fast Forward 30 seconds
</button>
<time class="ssp-timer">00:00</time>
/
<!-- We need actual duration here from the server -->
<time class="ssp-duration" datetime="PT0H2M13S">2:13</time>
<nav class="player-panels-nav">
<button class="subscribe-btn" id="subscribe-btn-21129" title="Subscribe">Subscribe</button>
<button class="share-btn" id="share-btn-21129" title="Share">Share</button>
</nav>
RSS Feed
<input value="https://dmarcreport.com/feed/podcast/dmarc-report" class="input-rss input-rss-21129" title="RSS Feed URL" readonly />
<button class="copy-rss copy-rss-21129" title="Copy RSS Feed URL" aria-label="Copy RSS Feed URL"></button>
Share
<a href="https://www.facebook.com/sharer/sharer.php?u=https://dmarcreport.com/blog/podcast/cybercriminals-target-x-nigeria-fights-cyberattacks-threat-actors-attack/&t=Cybercriminals Target X, Nigeria Fights Cyberattacks, Threat Actors Attack" target="blank" rel="noopener noreferrer" class="share-icon facebook" title="Share on Facebook">
</a>
<a href="https://twitter.com/intent/tweet?text=https://dmarcreport.com/blog/podcast/cybercriminals-target-x-nigeria-fights-cyberattacks-threat-actors-attack/&url=Cybercriminals Target X, Nigeria Fights Cyberattacks, Threat Actors Attack" target="blank" rel="noopener noreferrer" class="share-icon twitter" title="Share on Twitter">
</a>
<a href="https://media.mailhop.org/dmarcreport/images/2025/02/Cybercriminals-Target-X-Nigeria-Fights-Cyberattacks-Threat-Actors-Attack.mp3" target="blank" rel="noopener noreferrer" class="share-icon download" title="Download" download>
</a>
Link
<input value="https://dmarcreport.com/blog/podcast/cybercriminals-target-x-nigeria-fights-cyberattacks-threat-actors-attack/" class="input-link input-link-21129" title="Episode URL" readonly />
<button class="copy-link copy-link-21129" title="Copy Episode URL" aria-label="Copy Episode URL" readonly=""></button>
Embed
/*! This file is auto-generated */ ’ title=“Embed Code” class=“input-embed input-embed-21129” readonly/>
<button class="copy-embed copy-embed-21129" title="Copy Embed Code" aria-label="Copy Embed Code"></button>
A fresh new month, a brand new starting. Yes, it is the month of February, and some of you are aiming to crush your Q1 2025 goals, while others are getting a bit tired of the 2025 New Year resolution rush. Businesses, brands, and e-commerce platforms are running lucrative offers to lure consumers into splurging their **hard-earned money on retail therapy.
Unfortunately, threat actors are lurking around, waiting for that one careless click or that ignorant download you make, which will help them invade your system. So, businesses and individuals, be highly cautious of all those **emails and messages that you receive. Know that only your knowledge and caution can save you from those malicious cyberattacks.
It’s the first bulletin of the month, and this week, we are going to talk about the recent attacks on the high-profile X accounts. We will also focus on how Nigeria is standing tall and strong amidst the increasing cybercrime attacks across Africa. Lastly, we will try to understand why certain cybercriminals are targeting the Microsoft ADFS.
Let’s not wait anymore!
Cybercriminals targeting high-profile X accounts for committing crypto fraud!
There’s a one-click phishing campaign doing the rounds on X (formerly Twitter). Threat actors are targeting high-profile X users such as political figures, renowned journalists, and X employees. The core idea is to hijack their profiles and then carry out cryptocurrency fraud. Sentinel Labs uncovered this ongoing threat attack that is dominant on X.
However, they believe that the threat campaign can also be spread across other social media platforms . The cybercriminals basically want to leverage the reach of all these big accounts. Scammers hack into these **high-impact accounts so that they can easily target naive people with crypto scams to make some quick and easy money.
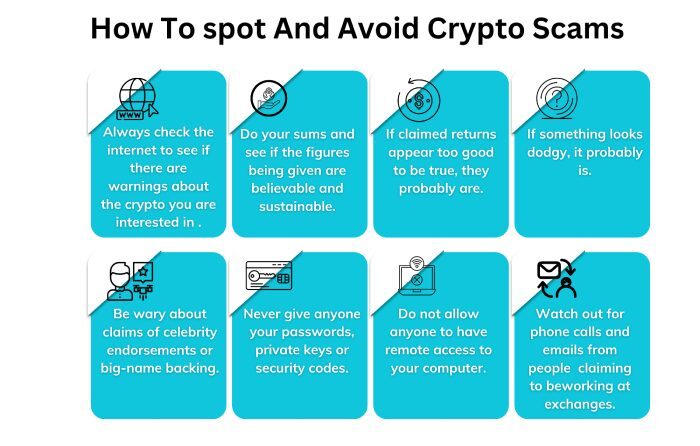
The moment a hacker gains access to any of these high-profile accounts, they lock out the legitimate user and start posting fraudulent and misguiding cryptocurrency opportunities. They can even share external links to malicious websites. These websites are designed with crypto-theft-related themes to attract additional targets. The main reason behind targeting high impact profiles on X is to reach out to a wider audience base as well as maximize their financial gain.
Threat actors are using different types of phishing lures, such as the ‘account login’ notice through emails, to make users believe that someone has logged into their X account from an unfamiliar device. A malicious link is also shared, clicking upon which scammers will gain access to your X credentials.
Similarly, copyright-violation emails are also sent out to create a sense of panic among the users, whereby the users are asked to share their credentials.
Nigeria stands tall against cyberattacks!
Africa is currently grappling with increasing cases of cyberattacks. However, Nigeria has decided to combat cybercriminals more strictly. In the past year, Nigerian authorities have arrested over 1000 threat actors who were involved in cyber frauds and scams. EFCC, or the **Economic and Financial Crimes Commission in Nigeria, has prosecuted around 42 foreign nationals who had allegedly carried out romance and cryptocurrency frauds. Nigerian authorities had also carried out a massive raid to bust a cybercrime syndicate of around 800 people.
Nigeria is standing tall against the threat actors at a time when the entire **African continent is experiencing over 3200 attacks every week. Ethiopia tops the chart as the riskiest country in Africa for cybercrime, while Nigeria comes at number 19 .
Experts believe that Africa is highly prone to cyberattacks as compared to other countries. The reason beyond this is **rapid digitization and lack of skilled workforce. As of now, there are only 20,000 qualified cybersecurity engineers across the continent. Experts have also witnessed a special trend in which some of the threat actors prefer testing their new malicious tactics in African countries first before attacking other nations.
Threat actors attack Microsoft Active Directory Federation Services
**Experts at Abnormal Security have recently found out that a sophisticated campaign is being run to exploit Microsoft’s ADFS in order to break into the multifactor authentication system and gain access to Microsoft user accounts. Currently, the threat actors are focusing on 150 organizations. The majority of these are educational establishments that depend primarily on ADFS for authentication processes across different cloud-based and on-premise systems .
Threat actors continue to target Microsoft Active Directory Federation Services (ADFS), making it crucial for organizations to implement strong cybersecurity measures, including email authentication protocols like DMARC, SPF, and DKIM, to mitigate phishing and spoofing attacks.
The high-end campaign leverages spoofed emails, which direct naive users to malicious Microsoft ADFS log-in pages. The moment a victim enters their credentials and shares the MFA code, threat actors get easy access to that particular account. Potential targets of this sophisticated campaign get fake emails that appear to be coming from Microsoft’s IT help desk. The emails often carry a sense of urgency and compel the users to have a look at something that requires their immediate attention.

Operations Lead
Operations Lead at DuoCircle. Runs project management, developer coordination, and technical support execution for DMARC Report.
LinkedIn Profile →Take control of your DMARC reports
Turn raw XML into actionable dashboards. Start free - no credit card required.