Understanding credential phishing and the role of DMARC in defense

Quick Answer
_According to the FBI's 2022 Internet Crime Report (IC3), 300,497 US-based victims reported phishing incidents in a single year, and Business Email Compromise (BEC) caused more than $2.7 billion in direct losses. DMARC Report Understanding credential phishing and the role of DMARC in defense
Related: Free DMARC Checker ·How to Create an SPF Record ·SPF Record Format

Try Our Free DMARC Checker
Validate your DMARC policy, check alignment settings, and verify reporting configuration.
Check DMARC Record →The support tickets we get after a spoofing incident all start the same way: ‘we didn’t know someone was sending email from our domain,’ says Vasile Diaconu, Operations Lead at DuoCircle. DMARC reporting would have caught it weeks earlier. The cost of monitoring is nothing compared to the cost of a successful impersonation attack.
_According to the FBI’s 2022 Internet Crime Report (IC3), 300,497 US-based victims reported phishing incidents in a single year, and Business Email Compromise (BEC) caused more than $2.7 billion in direct losses. DMARC Report
Understanding credential phishing and the role of DMARC in defense
<button title="Play" aria-label="Play Episode" aria-pressed="false" class="play-btn">
Play Episode
</button>
<button title="Pause" aria-label="Pause Episode" aria-pressed="false" class="pause-btn hide">
Pause Episode
</button>
<audio preload="none" class="clip clip-14235">
<source src="https://media.mailhop.org/dmarcreport/images/2024/07/Understanding-credential-phishing-and-the-role-of-DMARC-in-defense.mp3">
</audio>
<button class="player-btn player-btn__volume" title="Mute/Unmute">
Mute/Unmute Episode
</button>
<button data-skip="-10" class="player-btn player-btn__rwd" title="Rewind 10 seconds">
Rewind 10 Seconds
</button>
<button data-speed="1" class="player-btn player-btn__speed" title="Playback Speed" aria-label="Playback Speed">1x</button>
<button data-skip="30" class="player-btn player-btn__fwd" title="Fast Forward 30 seconds">
Fast Forward 30 seconds
</button>
<time class="ssp-timer">00:00</time>
/
<!-- We need actual duration here from the server -->
<time class="ssp-duration" datetime="PT0H2M9S">2:09</time>
<nav class="player-panels-nav">
<button class="subscribe-btn" id="subscribe-btn-14235" title="Subscribe">Subscribe</button>
<button class="share-btn" id="share-btn-14235" title="Share">Share</button>
</nav>
RSS Feed
<input value="https://dmarcreport.com/feed/podcast/dmarc-report" class="input-rss input-rss-14235" title="RSS Feed URL" readonly />
<button class="copy-rss copy-rss-14235" title="Copy RSS Feed URL" aria-label="Copy RSS Feed URL"></button>
Share
<a href="https://www.facebook.com/sharer/sharer.php?u=https://dmarcreport.com/blog/podcast/understanding-credential-phishing-and-the-role-of-dmarc-in-defense/&t=Understanding credential phishing and the role of DMARC in defense" target="blank" rel="noopener noreferrer" class="share-icon facebook" title="Share on Facebook">
</a>
<a href="https://twitter.com/intent/tweet?text=https://dmarcreport.com/blog/podcast/understanding-credential-phishing-and-the-role-of-dmarc-in-defense/&url=Understanding credential phishing and the role of DMARC in defense" target="blank" rel="noopener noreferrer" class="share-icon twitter" title="Share on Twitter">
</a>
<a href="https://media.mailhop.org/dmarcreport/images/2024/07/Understanding-credential-phishing-and-the-role-of-DMARC-in-defense.mp3" target="blank" rel="noopener noreferrer" class="share-icon download" title="Download" download>
</a>
Link
<input value="https://dmarcreport.com/blog/podcast/understanding-credential-phishing-and-the-role-of-dmarc-in-defense/" class="input-link input-link-14235" title="Episode URL" readonly />
<button class="copy-link copy-link-14235" title="Copy Episode URL" aria-label="Copy Episode URL" readonly=""></button>
Embed
/*! This file is auto-generated */ ’ title=“Embed Code” class=“input-embed input-embed-14235” readonly/>
<button class="copy-embed copy-embed-14235" title="Copy Embed Code" aria-label="Copy Embed Code"></button>
Your passwords and login details are literally and figuratively the key to your personal and professional accounts , which include everything from your bank details to your important documents. Now, imagine what would happen if your login credentials fell into the hands of cybercriminals. Unfortunately, it’s not just a hypothetical scenario. Attackers use sophisticated strategies to deceive you into divulging sensitive information through a technique called credential phishing.
You would be surprised to know that this trick isn’t new; in fact, its roots can be traced back to the early days of email communication. The only difference between the techniques of then and now is the way these attacks are being executed. Today, thanks to **cutting-edge technologies like artificial intelligence, machine learning, behavioral analytics, etc, these scams are more convincing and sophisticated than ever.
What is credential phishing?
You might have heard of various types of phishing attacks, like spear phishing and vishing. Credential phishing is one such technique that capitalizes on human trust to steal your credentials. The technique has been spreading like a plague with devastating impact, so much so that an IBM report highlighted that in 2023, credential phishing attacks were the second most costly attacks of them all.
This type of social engineering attack targets and tricks unsuspecting users into believing that they are communicating with a genuine email sender or website, compelling them to reveal sensitive information like usernames, passwords, credit card details, etc. The emails sent by the attackers are curated in a way that they bypass spam filters and appear as if they’re from legitimate organizations. The moment you click one of the links inside the email, you will be routed to a fraudulent webpage, which can steal your sensitive information, such as banking or corporate credentials.
Generally, threat actors prey on the following credentials, which serve as lucrative targets for their malicious activities:
-
**Banking credentials: **These are particularly valuable to the attackers as these details can be used to transfer money from the victim’s account or conduct fraudulent transactions.
-
**Corporate credentials: **By entering a company’s internal systems, the cybercriminals steal sensitive data such as financial records, employee information, and proprietary intellectual property .

Whether it is your bank details or your company’s important information, the perpetrators follow a common route to trespass your defenses, that is, by creating a false sense of urgency among the email recipients. That is to say, as soon as you come across a message that requires you to act promptly, chances are you might ignore the red flags and eventually fall prey to the attackers’ tactics. Such emails often direct you to a phishing site where entering your credentials can lead to significant security breaches.
What is the impact of credential phishing on businesses?
Being a credential phishing attack target certainly takes a toll on your bottom line, but there’s more to it than meets the eye. Like with any other cyberattack, the implications of this type of attack extend beyond immediate financial losses. Such attacks can lead to your customers not trusting you with their personal information. This loss can ultimately result in them taking their business elsewhere and tarnishing your brand’s reputation.
From an operational perspective, recovering from a credential phishing incident is resource-intensive. The kind of time, effort, and resources you will have put into a security overhaul will not only be exorbitant but can also disrupt normal business operations and lead to downtime. Apart from this, credential phishing can expose your business to legal repercussions . If customer data is compromised, you could face lawsuits or hefty fines for failing to comply with data protection laws. These legal challenges not only increase costs but also damage the **business’s reputation further.
What is the role of DMARC in preventing credential phishing?
To keep cyber attackers from gaining access to your sensitive information, it is important that you protect your email channel. A good way to do it is to authenticate your email-sending domains with an **authentication protocol like DMARC (Domain-based Message Authentication, Reporting, and Conformance).
This protocol works in conjunction with SPF (Sender Policy Framework) and DKIM (DomainKeys Identified Mail) to ensure that **emails claiming to be from your domain are legitimate.
Let us take a look at how **DMARC configuration can help you prevent grave attacks like credential phishing:
Email authentication
DMARC is perhaps one of the most effective mechanisms to defend against cyberattacks as it builds upon SPF and DKIM. By leveraging these existing protocols, DMARC provides a strong framework for email servers to rely on when verifying the authenticity of incoming mail. It ensures that emails are indeed from the domains they claim to be from, helping to prevent email spoofing - a common tactic in phishing attacks.
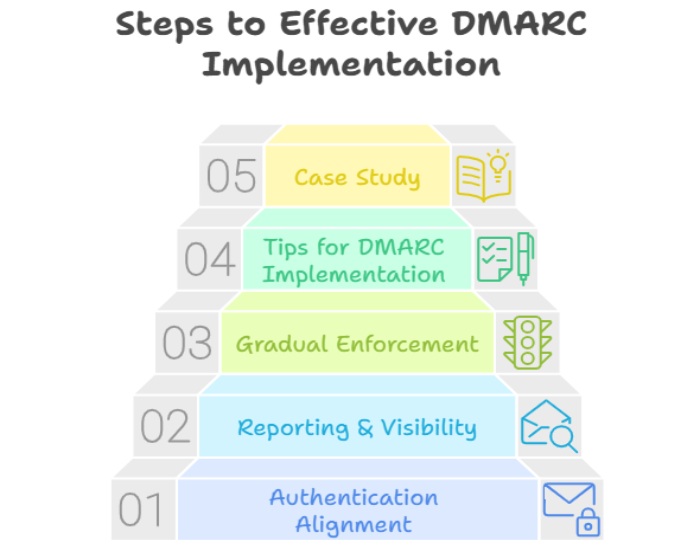
Policy enforcement
DMARC enables you to publish policies in your DNS record, which means that you can define what would happen to the emails that fail SPF and DKIM authentication. The policies can instruct receiving email servers to either do nothing, quarantine the message, or reject it outright. This means that if an email claiming to be from your domain fails these checks, it won’t reach the inbox of the person it was sent to.
Reporting
What makes DMARC the most robust protocol out of the three is perhaps its reporting feature. DMARC also provides a reporting mechanism that allows you to receive reports from email receivers. These reports give insights into which emails are passing SPF and DKIM checks and which are failing, helping you **detect and prevent misuse of your email domain.
While DMARC reports give you a comprehensive understanding of how your email authentication measures are performing, it can be tricky to decipher them, especially if you are from a non-technical background. This is why you need a DMARC report analyzer that allows you to read DMARC reports and analyze them properly.
Want to get started on protecting your organization from credential phishing with DMARC reporting? You’re in the right place! For all your small or large-scale reporting needs, get in touch with our team at DMARCReport today!
Topics

General Manager
Founder and General Manager of DuoCircle. Product strategy and commercial lead for DMARC Report's 2,000+ customer base.
LinkedIn Profile →Take control of your DMARC reports
Turn raw XML into actionable dashboards. Start free - no credit card required.