Role of DMARC in detecting and preventing shadow IT

Quick Answer
DMARC (RFC 7489) ties SPF and DKIM together by requiring alignment between the envelope sender and the visible `From` header. According to Google's February 2024 bulk sender requirements, a DMARC policy of at least `p=none` is now mandatory for any domain sending 5,000+ messages per day to Gmail users. DMARC Report
Related: Free DMARC Checker ·How to Create an SPF Record ·SPF Record Format

Try Our Free DMARC Checker
Validate your DMARC policy, check alignment settings, and verify reporting configuration.
Check DMARC Record →
The organizations that invest in email authentication early save themselves from expensive incidents later, says Vasile Diaconu, Operations Lead at DuoCircle. We see the pattern constantly: a domain gets spoofed, customers lose trust, and the remediation effort costs 10x what proactive DMARC setup would have cost.
DMARC (RFC 7489) ties SPF and DKIM together by requiring alignment between the envelope sender and the visible From header. According to Google’s February 2024 bulk sender requirements, a DMARC policy of at least p=none is now mandatory for any domain sending 5,000+ messages per day to Gmail users.
DMARC Report
Role of DMARC in detecting and preventing shadow IT
<button title="Play" aria-label="Play Episode" aria-pressed="false" class="play-btn">
Play Episode
</button>
<button title="Pause" aria-label="Pause Episode" aria-pressed="false" class="pause-btn hide">
Pause Episode
</button>
<audio preload="none" class="clip clip-15513">
<source src="https://media.mailhop.org/dmarcreport/images/2024/09/Role-Of-DMARC-In-Detecting-And-Preventing-Shadow-IT.mp3">
</audio>
<button class="player-btn player-btn__volume" title="Mute/Unmute">
Mute/Unmute Episode
</button>
<button data-skip="-10" class="player-btn player-btn__rwd" title="Rewind 10 seconds">
Rewind 10 Seconds
</button>
<button data-speed="1" class="player-btn player-btn__speed" title="Playback Speed" aria-label="Playback Speed">1x</button>
<button data-skip="30" class="player-btn player-btn__fwd" title="Fast Forward 30 seconds">
Fast Forward 30 seconds
</button>
<time class="ssp-timer">00:00</time>
/
<!-- We need actual duration here from the server -->
<time class="ssp-duration" datetime="PT0H2M7S">2:07</time>
<nav class="player-panels-nav">
<button class="subscribe-btn" id="subscribe-btn-15513" title="Subscribe">Subscribe</button>
<button class="share-btn" id="share-btn-15513" title="Share">Share</button>
</nav>
RSS Feed
<input value="https://dmarcreport.com/feed/podcast/dmarc-report" class="input-rss input-rss-15513" title="RSS Feed URL" readonly />
<button class="copy-rss copy-rss-15513" title="Copy RSS Feed URL" aria-label="Copy RSS Feed URL"></button>
Share
<a href="https://www.facebook.com/sharer/sharer.php?u=https://dmarcreport.com/blog/podcast/role-of-dmarc-in-detecting-and-preventing-shadow-it/&t=Role of DMARC in detecting and preventing shadow IT " target="blank" rel="noopener noreferrer" class="share-icon facebook" title="Share on Facebook">
</a>
<a href="https://twitter.com/intent/tweet?text=https://dmarcreport.com/blog/podcast/role-of-dmarc-in-detecting-and-preventing-shadow-it/&url=Role of DMARC in detecting and preventing shadow IT " target="blank" rel="noopener noreferrer" class="share-icon twitter" title="Share on Twitter">
</a>
<a href="https://media.mailhop.org/dmarcreport/images/2024/09/Role-Of-DMARC-In-Detecting-And-Preventing-Shadow-IT.mp3" target="blank" rel="noopener noreferrer" class="share-icon download" title="Download" download>
</a>
Link
<input value="https://dmarcreport.com/blog/podcast/role-of-dmarc-in-detecting-and-preventing-shadow-it/" class="input-link input-link-15513" title="Episode URL" readonly />
<button class="copy-link copy-link-15513" title="Copy Episode URL" aria-label="Copy Episode URL" readonly=""></button>
Embed
/*! This file is auto-generated */ ’ title=“Embed Code” class=“input-embed input-embed-15513” readonly/>
<button class="copy-embed copy-embed-15513" title="Copy Embed Code" aria-label="Copy Embed Code"></button>
Have you wondered why some organizations have stringent policies that prevent them from using certain apps and devices to get work done while others are pretty open with no such restrictions? In the latter situation, the employees certainly have more flexibility and convenience, but this openness can introduce significant security risks.
This phenomenon, known as shadow IT, refers to the use of unauthorized technology within an organization. Without due vigilance, these tools are sure to open doors to security breaches, data leaks, or compliance issues. So, does this mean that organizations that offer flexibility are doomed to face these risks? Not really.
As far as finding this balance between **security and operational freedom goes, DMARC (Domain-based Message Authentication, Reporting & Conformance) is an important step.
In this article, we will dig deeper into what shadow IT is and how DMARC detects and prevents security risks associated with it.
What Is shadow IT?
Shadow IT refers to the use of unauthorized hardware, software, or cloud services for official purposes without the due approval/knowledge of the IT team of your organization. There are a number of factors that motivate employees to rely on shadow IT to get work done. This includes remote working, which, in many cases, involves using **personal devices and apps that have not been approved by the department.
Apart from this, if the IT team is slow to respond to trouble reports or refuses to update outdated systems, employees may seek faster, alternative solutions. Encouraging employees to track their time can help identify inefficiencies that often lead to the use of shadow IT.
Considering these situations, no doubt, shadow IT enhances **productivity and innovation but also introduces significant security and compliance risks. This is because such unauthorized tools do not guarantee security like an approved system within the organization, exposing the organization to data breaches and many other cyber issues.
The risks of shadow IT
With the rise of remote working, the ease of convenience that cloud services offer , and the proliferation of email communication, shadow IT has become a thing of concern for many organizations, particularly their IT and security teams.
Looking beyond the immediate benefits, there are several serious risks of shadow IT that you should know about. Let us take a look at some of them:
Risk of security breaches
Most unsanctioned tools and applications lack strong security features, making them a haven for cyberattacks. In most cases, these tools bypass certain protocols set forth by the organization, leaving them vulnerable to exploitation. What’s worse, hackers identify these **loopholes and strategically target them to get through the network, steal sensitive data, and cause significant disruptions.
That is to say, if you do not keep an eye on your shadow IT landscape, you are letting the organization’s attack surface expand and increase the risk of malware infections, data breaches, and other cyber threats.
Inefficient data governance
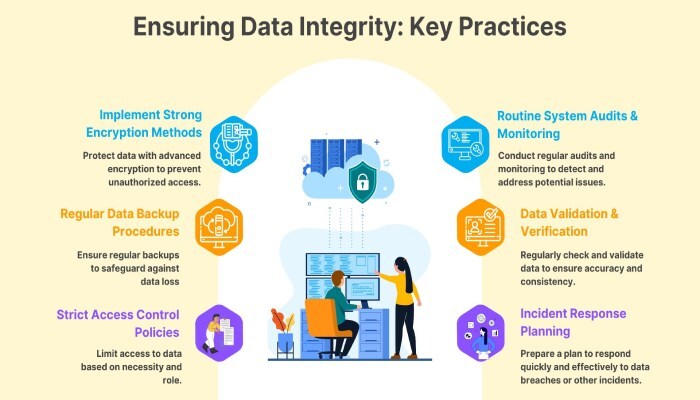
With shadow IT, comes the possibility of storing and processing data in unauthorized applications, which inevitably leads to inefficient data governance. This lack of centralization in **control and oversight further makes it challenging to enforce data management policies while ensuring data integrity. Such a scattered approach may further result in inconsistencies, data loss, or problems with retrieving the same.
Not to mention, if your data is all over the place across different unauthorized platforms, it becomes quite complex and difficult to ensure compliance with data protection regulations, perform audits, or effectively monitor the use of data.
Increased email security risks
It is no doubt that email is one of the most critical aspects of business communication, but it is as vulnerable as it is vital. So, introducing **email services and tools used in shadow IT only increases its susceptibility to cyber threats, especially because they lack essential security features such as encryption, spam filtering, and phishing detection.
Attackers try to make the most of this opportunity to distribute malware, launch phishing attacks, and impersonate company personnel.
Inability to properly patch
Here’s something you should know: no system or network is immune to malicious attacks. Patching is considered to be an integral aspect of any reliable security strategy. However, when it comes to patching (updating systems and devices with the latest security fixes), the unsanctioned systems and tools often miss out on important updates. This makes them vulnerable to attacks, causing potential crashes and performance issues. If patches are misapplied or done at the wrong time, it can lead to even more problems.
Enhancing security with DMARC
DMARC is an often-talked-about protocol in the cybersecurity landscape, and for good reason. It helps reduce the volume of spam and other malicious emails by protecting against unauthorized use of your email domain through the **enforcement of rigid policies and ensuring that only authorized servers deliver emails from that domain.
Let us take a look at how DMARC detects and prevents risks that come with shadow IT.
How Do You Prevent shadow IT with DMARC?
-
Authentication enforcement: DMARC verifies that emails are sent from authorized servers , preventing unauthorized use of your domain.
-
Policy specification: DMARC allows you to keep a tab on the emails that fail SPF and DKIM checks by specifying DMARC policies to none, reject, or quarantine, thereby managing unauthorized email use that happens through shadow IT infrastructure.
How Do You Detect Shadow IT with DMARC?
-
Aggregate reports: DMARC generates reports that provide insights into all email traffic using your domain. These reports help identify unauthorized or suspicious email activity, indicating potential shadow IT use.
-
Forensic reports: Forensic reports offer detailed information on emails that fail DMARC checks, highlighting attempts to **use unauthorized technology for malicious purposes.
**DMARCReport is here to help you bolster your defenses If your organization offers the flexibility to use third-party resources, managing and preventing shadow IT shouldn’t be an issue anymore. Thanks to DMARC, you can now secure your email communications and maintain control over your domain’s email usage. With DMARC by your side, you gain visibility into your email traffic, identify unauthorized platforms, and enforce security policies effectively. Struggling to find the right balance between flexibility and security? Request a demo today to learn how your organization can stay protected from email-based threats.
Topics

General Manager
Founder and General Manager of DuoCircle. Product strategy and commercial lead for DMARC Report's 2,000+ customer base.
LinkedIn Profile →Take control of your DMARC reports
Turn raw XML into actionable dashboards. Start free - no credit card required.