What Is Dumpster Diving in Cybersecurity?
A Detailed Guide by DMARCReport
Cybersecurity discussions often focus on advanced threats such as phishing campaigns, ransomware, domain spoofing, or zero-day vulnerabilities. However, not every data breach begins with complex code or technical exploits. Some attacks start with something far simpler—searching through discarded trash. This method, known as dumpster diving, remains a surprisingly effective tactic for gathering sensitive information.
At DMARCReport, we emphasize that true cybersecurity extends beyond firewalls and authentication protocols. Protecting digital identities, domains, and communication channels is essential, but physical data exposure can undermine even the most advanced security infrastructure. Dumpster diving demonstrates how physical negligence can quickly transform into digital compromise.
This guide explores what dumpster diving means in cybersecurity, how attackers use it, why it remains relevant, and how organizations can defend against it.

Understanding Dumpster Diving in Cybersecurity
Dumpster diving in cybersecurity refers to the act of searching through discarded materials—such as trash bins, recycling containers, or improperly disposed storage devices—to retrieve sensitive information. Attackers look for documents, credentials, financial records, or hardware that may provide insight into a person or organization.
Although the name suggests rummaging through physical dumpsters, the concept is broader. It includes retrieving unshredded documents, outdated hard drives, USB drives, printed internal reports, or even handwritten notes containing passwords. Essentially, attackers target anything that has been thrown away without proper destruction.
Unlike hacking attempts that require technical skills, dumpster diving often requires nothing more than patience and access. It is a low-cost, low-risk entry point for attackers who want to gather intelligence before launching a more targeted cyberattack.
Why Dumpster Diving Still Poses a Threat
Many organizations invest heavily in cybersecurity technologies such as intrusion detection systems, endpoint protection, and email authentication standards like DMARC. Yet physical security practices sometimes lag behind digital defenses. That gap creates opportunity.
Dumpster diving remains effective because:
- It exploits human oversight rather than software vulnerabilities.
- It provides contextual information useful for social engineering.
- It often goes unnoticed until after damage occurs.
- It bridges physical and digital security weaknesses.
Even in modern workplaces that rely on cloud platforms and encrypted communication, paper documents and physical storage devices still exist. Employee directories, vendor contracts, printed reports, invoices, HR files, and meeting notes frequently make their way into standard trash bins.
When such materials are not securely destroyed, they become valuable intelligence sources.

Types of Information Attackers Look For
Dumpster diving is rarely random. Attackers typically have a goal in mind, whether that goal is financial fraud, identity theft, corporate espionage, or preparing for a phishing campaign. The type of information they seek includes:
- Personal Identifiable Information (PII): Discarded mail, onboarding forms, or HR documents may contain names, addresses, dates of birth, Social Security numbers, or identification details.
- Login Credentials: Sticky notes, printed password lists, configuration documents, or onboarding guides may expose usernames and temporary passwords.
- Financial Records: Invoices, bank statements, transaction summaries, or payment authorizations can provide insight into financial processes.
- Corporate Intelligence: Internal memos, strategy plans, vendor contracts, and employee contact lists can help attackers map an organization’s structure.
- Outdated Digital Media: Old hard drives, USB drives, CDs, or backup tapes that were not properly wiped can still contain recoverable data.
Even fragmented information can be useful. Attackers often piece together small details to create a comprehensive profile. A printed phone list combined with a discarded meeting agenda might provide everything needed to impersonate an executive convincingly.
How Dumpster Diving Fuels Cyberattacks
Dumpster diving is rarely the final step. It is usually part of a larger strategy.
Social Engineering
Social engineering attacks rely on trust manipulation. The more details an attacker has, the more believable their impersonation becomes. Information collected from discarded documents can provide:
- Names of department heads
- Project timelines
- Vendor relationships
Internal terminology
With this knowledge, attackers can craft convincing phishing emails or business email compromise schemes. They may reference real projects, mimic authentic communication styles, or impersonate known suppliers.
For example, if a discarded invoice reveals a recurring vendor payment, an attacker could send a fraudulent payment request that appears legitimate. Without suspicion, employees may comply.

Identity Theft
Dumpster diving is also a direct pathway to identity theft. Personal documents thrown away without shredding can allow criminals to open financial accounts, apply for loans, or conduct fraudulent transactions.
Even partial information—such as the last four digits of an identification number combined with a full name and address—can significantly increase the risk of impersonation.
Corporate Espionage
In competitive industries, access to internal documentation can reveal product development plans, marketing strategies, or partnership negotiations. Competitors or malicious actors may exploit discarded materials to gain strategic advantages.
Common Misconceptions About Dumpster Diving
There are several misconceptions that contribute to continued vulnerability.
First, many assume that cybersecurity threats exist only online. While digital attacks are common, physical data exposure can be just as damaging. A printed password sheet can bypass sophisticated encryption measures.
Second, some believe tearing documents in half is sufficient. In reality, partially destroyed documents can be reconstructed. Determined attackers have reassembled shredded papers to retrieve critical information.
Third, organizations may assume that trash located on private property is safe. However, dumpsters in accessible areas—especially those without locks—can still be reached by unauthorized individuals.
Finally, some think that outdated hardware holds no value. In truth, improperly wiped drives can retain large volumes of sensitive data long after being discarded.
Legal and Ethical Considerations
Dumpster diving exists in a complex legal landscape. In some jurisdictions, trash left in public areas may not carry an expectation of privacy. However, accessing locked dumpsters or trespassing on private property may constitute a criminal offense.
Regardless of legality, the ethical implications are clear: retrieving sensitive information for malicious purposes is a serious violation of privacy and security principles.
Organizations should not rely on legal ambiguity to protect their data. Proactive prevention is far more effective than legal recourse after a breach.
Preventing Dumpster Diving Attacks
Effective prevention requires combining policy, technology, and employee awareness.
Establish a Clear Disposal Policy
Organizations should develop formal policies outlining how sensitive materials must be discarded. This includes guidelines for paper records, digital storage devices, and obsolete hardware.
Retention schedules should define what must be archived and what must be securely destroyed.
Use High-Security Shredding
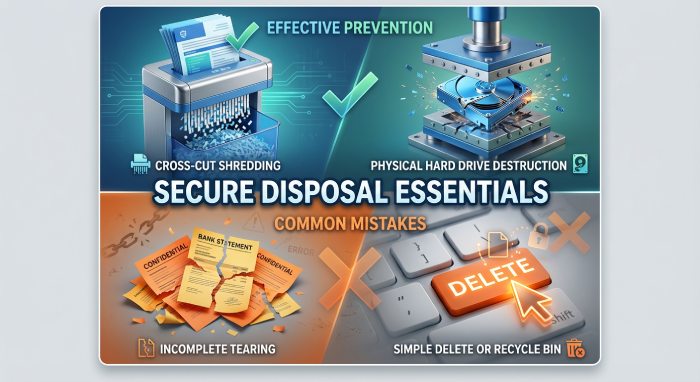
Cross-cut shredders provide significantly better protection than strip shredders. Documents containing sensitive information should always be shredded before disposal.
For high-risk industries, professional document destruction services may be appropriate.
Secure Electronic Media
Before discarding electronic devices, data must be securely erased using certified wiping tools. In cases involving highly sensitive information, physical destruction—such as degaussing or shredding storage media—may be necessary.
Simply deleting files or formatting drives is not sufficient.
Protect Waste Storage Areas
Dumpsters and recycling bins should be placed in secured, monitored areas. Lockable enclosures reduce the risk of unauthorized access.
Limiting access to disposal areas is a simple yet often overlooked defense.
Train Employees Regularly
Employee awareness is critical. Staff members should understand:
- What qualifies as sensitive data
- Why secure disposal matters
- How physical data leaks can lead to digital breaches
Training programs should reinforce the connection between physical security and cybersecurity.
Integrating Physical Security with Digital Protection
At DMARCReport, we emphasize holistic security. Email authentication protocols like DMARC help prevent spoofing and phishing, but they cannot compensate for exposed credentials found in discarded paperwork.
Security should be viewed as an interconnected ecosystem. Physical safeguards, data handling policies, employee training, and digital protections must work together.
Dumpster diving highlights an important lesson: attackers will exploit the weakest link. If technical defenses are strong, they may look for easier entry points in overlooked physical processes.

Final Thoughts
Dumpster diving may appear outdated compared to advanced cyberattacks, yet it remains highly relevant. The simplicity of the method makes it accessible, and the information gathered can enable significant damage.
Sensitive data does not lose its value simply because it has been discarded. Without proper destruction, trash becomes a source of intelligence for malicious actors.
Organizations and individuals must recognize that cybersecurity does not end at the network perimeter. Secure disposal practices, employee awareness, and integrated security policies are essential components of modern risk management.
At DMARCReport, we encourage a comprehensive approach to security—one that protects digital identities, communication channels, and physical information alike. By addressing both digital and physical vulnerabilities, businesses can significantly reduce their exposure to preventable threats.







