Beware of Phishing Attempts- Apple Users’ Version!

Quick Answer
_According to the FBI's 2022 Internet Crime Report (IC3), 300,497 US-based victims reported phishing incidents in a single year, and Business Email Compromise (BEC) caused more than $2.7 billion in direct losses. DMARC Report Beware of Phishing Attempts- Apple Users’ Version!

The support tickets we get after a spoofing incident all start the same way: ‘we didn’t know someone was sending email from our domain,’ says Vasile Diaconu, Operations Lead at DuoCircle. DMARC reporting would have caught it weeks earlier. The cost of monitoring is nothing compared to the cost of a successful impersonation attack.
_According to the FBI’s 2022 Internet Crime Report (IC3), 300,497 US-based victims reported phishing incidents in a single year, and Business Email Compromise (BEC) caused more than $2.7 billion in direct losses. DMARC Report
Beware of Phishing Attempts- Apple Users’ Version!
<button title="Play" aria-label="Play Episode" aria-pressed="false" class="play-btn">
Play Episode
</button>
<button title="Pause" aria-label="Pause Episode" aria-pressed="false" class="pause-btn hide">
Pause Episode
</button>
<audio preload="none" class="clip clip-12478">
<source src="https://media.mailhop.org/dmarcreport/images/2024/04/Beware-of-Phishing-Attempts-Apple-Users-Version.mp3">
</audio>
<button class="player-btn player-btn__volume" title="Mute/Unmute">
Mute/Unmute Episode
</button>
<button data-skip="-10" class="player-btn player-btn__rwd" title="Rewind 10 seconds">
Rewind 10 Seconds
</button>
<button data-speed="1" class="player-btn player-btn__speed" title="Playback Speed" aria-label="Playback Speed">1x</button>
<button data-skip="30" class="player-btn player-btn__fwd" title="Fast Forward 30 seconds">
Fast Forward 30 seconds
</button>
<time class="ssp-timer">00:00</time>
/
<!-- We need actual duration here from the server -->
<time class="ssp-duration" datetime="PT0H1M37S">1:37</time>
<nav class="player-panels-nav">
<button class="subscribe-btn" id="subscribe-btn-12478" title="Subscribe">Subscribe</button>
<button class="share-btn" id="share-btn-12478" title="Share">Share</button>
</nav>
RSS Feed
<input value="https://dmarcreport.com/feed/podcast/dmarc-report" class="input-rss input-rss-12478" title="RSS Feed URL" readonly />
<button class="copy-rss copy-rss-12478" title="Copy RSS Feed URL" aria-label="Copy RSS Feed URL"></button>
Share
<a href="https://www.facebook.com/sharer/sharer.php?u=https://dmarcreport.com/blog/podcast/beware-of-phishing-attempts-apple-users-version/&t=Beware of Phishing Attempts- Apple Users’ Version!" target="blank" rel="noopener noreferrer" class="share-icon facebook" title="Share on Facebook">
</a>
<a href="https://twitter.com/intent/tweet?text=https://dmarcreport.com/blog/podcast/beware-of-phishing-attempts-apple-users-version/&url=Beware of Phishing Attempts- Apple Users’ Version!" target="blank" rel="noopener noreferrer" class="share-icon twitter" title="Share on Twitter">
</a>
<a href="https://media.mailhop.org/dmarcreport/images/2024/04/Beware-of-Phishing-Attempts-Apple-Users-Version.mp3" target="blank" rel="noopener noreferrer" class="share-icon download" title="Download" download>
</a>
Link
<input value="https://dmarcreport.com/blog/podcast/beware-of-phishing-attempts-apple-users-version/" class="input-link input-link-12478" title="Episode URL" readonly />
<button class="copy-link copy-link-12478" title="Copy Episode URL" aria-label="Copy Episode URL" readonly=""></button>
Embed
/*! This file is auto-generated */ ’ title=“Embed Code” class=“input-embed input-embed-12478” readonly/>
<button class="copy-embed copy-embed-12478" title="Copy Embed Code" aria-label="Copy Embed Code"></button>
Lately, Apple users across 92 countries have received the biggest shock of their lives in their email and iPhone inboxes! Apple contacted them regarding a “mercenary spyware attack.” To make it more ominous, the users would get to see a “Threat notification” if they logged into their Apple ID.
The message emphasized the gravity of the warning and urged the users to **be serious about the threat. Apple did not share any further details to prevent the mercenary spyware from developing a security evasion tactic.
Notably, the emails and messages sent by Apple did not contain any links.
This is where you **need to be careful enough if you wish not to fall prey to cyber attacks such as phishing.
How Do You Know If The Apple Message You Got is Legitimate or Not?
This is something every Apple user must be aware of.
Apple has this support document that clearly mentions that all the emails and images that it sends out will carry no link at all. Also, these messages direct users to log in with their Apple ID right away. Once the users log into their Apple ID and click on the View Details link, they get directed to another page where they get to learn about the potential threat.
Also, the emails and messages are sent only to the email IDs and phone numbers that are associated with the receiver’s Apple ID.
If you ever come across an email or imessage from Apple mentioning a mercenary spyware attack with a link attached to it, know that it is a scam! Delete the email/message ASAP.
Phishing Scams Conducted By Threat Actors By Mimicking Apple!
Apple is a luxury brand, **incredibly popular among those who wish to flaunt their opulent social stature. However, this is the reason why more and more threat actors impersonate the tech giant.
One of the most popular tricks played by phishing actors is to send out emails to Apple users regarding any Apple purchase that you don’t recognize. Such emails come with attached malicious links. They try to persuade you to click on the link to check your **purchase history. 
In that case, come out of that email and check your actual purchase history to verify whether or not you have bought something accidentally. Even if you have bought something accidentally, you can easily get a resolution by reporting the issue in the “Report a problem” section.
_Another trick used by threat actors is to send out iCloud storage warning emails. During the Q4 2023, rounds of emails got circulated online claiming that the iCloud storage was full for some to the users. The spammy email claimed to offer a “ free iCloud storage upgrade ” for the users. The email urged the recipients to click on the malicious link attached.
What Do You Do If You Receive a Fraudulent Email?
First of all, if you receive an email from Apple which you think is fraudulent, straightaway mark it as spam.
Next, follow the step-by-step details to report the spammy email to the concerned authorities:
-
Forward the entire email with all the headers.
-
You can report the email to reportphishing@apwg.org and reportphishing@apple.com
How Likely It Is For Apple to Send a Text Message to Its Users?
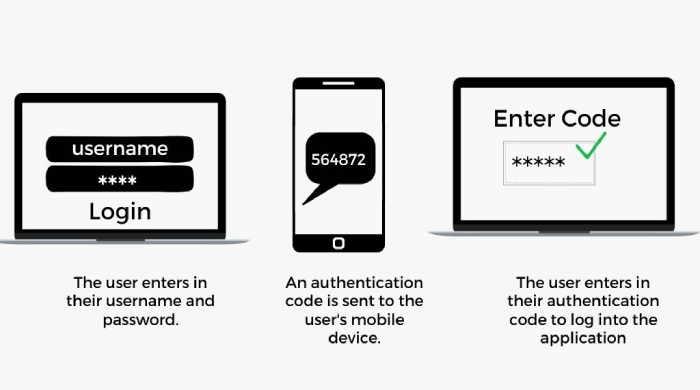
It is quite rare for Apple to send out text messages to its users on the Messages app. Even if it does, Apple relies on the two-factor authentication method to send text messages to the recipients. There is no possibility that Apple will send out **plain text messages to users.
Also, whenever you get any message from Apple, it will always show the **Verified Badge beside the Apple notification.
In case you get text messages that claim to be from Apple but don’t have any **Verification Badge with it, ignore the text and delete it right away. **Avoid clicking on any link that might have been sent with the text message.
Does Apple Call Its Users?
**Apple does NOT call the users until and unless you initiate the call for a tech support issue. Basically, when you connect with AppleCare, you get an option to receive a call back from their customer support executives.
However, if you start receiving multiple notifications asking you to give approval to a password reset, then it can be a case of MFA Bombing or Multi Factor Authentication bombing. The ultimate goal of the threat actors is to make you hit the “Allow” button accidentally. After that you may receive a call from a fake caller, posing to be an Apple support executive. The end goal is to reset your Apple ID password in all this confusion and chaos.
Every Apple user must be **well-versed in all the tactics deployed by threat actors so that these scammers can never succeed in breaking into their banks by impersonating Apple .
Get in touch with DMARCReport for any inquiries related to email security.
Topics

General Manager
Founder and General Manager of DuoCircle. Product strategy and commercial lead for DMARC Report's 2,000+ customer base.
LinkedIn Profile →Take control of your DMARC reports
Turn raw XML into actionable dashboards. Start free - no credit card required.