Prepare Ahead of Holiday Phishing Scams- The 2023 Holiday Season Guide

Quick Answer
The holiday season is here, but unfortunately, the [malicious scam season](https://www.mylondon.news/whats-on/whats-on-news/booking-travel-website-scam-phishing-27981382) is also right behind it. This is the time when cybercriminals are also geared up to trick people into buying things from [cloned websites](https://www.ncrypted.net/blog/what-is-website-cloning/), participating in fake contests promising exciting gifts, purchasing lottery tickets, etc.
Related: Free DMARC Checker

_According to the FBI’s 2022 Internet Crime Report (IC3), 300,497 US-based victims reported phishing incidents in a single year, and Business Email Compromise (BEC) caused more than $2.7 billion in direct losses. The holiday season is here, but unfortunately, the malicious scam season is also right behind it. This is the time when cybercriminals are also geared up to trick people into buying things from cloned websites, participating in fake contests promising exciting gifts, purchasing lottery tickets, etc.
Domain spoofing is trivially easy without DMARC enforcement, says Brad Slavin, General Manager of DuoCircle. Anyone can send email that looks like it comes from your domain. DMARC with p=reject is the only way to tell receiving servers to block unauthorized senders completely.
Do you know what’s the latest? It’s the puppy scam, scammers have started using the **holidays to fool people into paying off for pets that don’t exist or have some sort of medical issues they don’t disclose.
It’s also sad and scary to know that last year, the FBI reported a loss of $281 million to internet scams emerging from shopping and non-delivery schemes that **majorly spiked during the holiday season.
Common Scams to be Wary of This Holiday Season
Generally, consumers get trapped in the following types of scams that are active throughout the year but **shoot up significantly during the holiday times.

Fake or Cloned Online Stores
Users usually land on such bogus shopping platforms by clicking **advertisement links on social media and search engines._ The major red flags include heavily discounted items like a luxury bag available at one-fourth of the actual price_.
This way, your debit and credit cards can get compromised, or you won’t receive the item at all, not even the duped version!
Here’s a latest **real-life example of the same- Suzanne Kyle of Spruce Grove, Edmonton, fell victim to a holiday scam after purchasing a Christmas tree from Adjustabletrees.com. Despite appearing legitimate, the website turned out to be fraudulent, with Kyle losing CAD 1,500 . RCMP warns that the **well-designed site makes this type of fraud easy to fall for, as others have reported similar scams linked to the website.
Missed Delivery or Non-Delivery Notifications
It’s common for your family and friends to send you gifts during this time of the year. Taking advantage of the same fact, scammers send fake delivery emails or text messages to alert you of a missed delivery.
If you click the link provided, you will likely be redirected to a phishing website or a page asking you to submit sensitive details.
Gift Card Scams
Bad actors trick people into buying counterfeit gift cards or using them to pay for **fake or non-existing goods and services. And in the end, you realize that instead of getting a gift card on sale, you received the one with no money value.
Fake Charities
Around the holidays, bad guys try to trick people into giving money through fake charities or online fundraisers. It can be tricky to tell if it’s a scam, so before giving money, **be super careful when picking a charity. If you’re donating online, check the charity really well, see if the Better Business Bureau approves , and look at the website address for signs of a scam, like wrong spelling or no contact info. It’s also critical to make sure the donation platform itself follows strict security practices. Tools like Donorbox prioritize donor protection with 24/7 monitoring, PCI compliance, and data encryption - so your contributions stay safe from fraud and cyber threats. For things like GoFundMe, find out about the person or group running it before you donate.
Phishing Emails or Texts
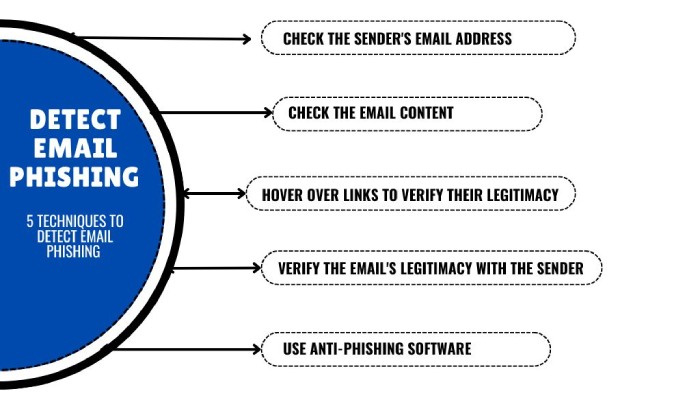
The chaos of the holiday season and the rush to buy gifts and **household items appear as a perfect breeding opportunity for phishing and spoofing experts. They send fraudulent emails and text messages, prompting you to click on **malicious links to share sensitive details or make_ _wire transfers.
A special note for companies, Threat actors often exploit domains of established companies to send fraudulent emails so that recipients trust them and take the desired step. So, it’s highly recommended that you shield your domains and business reputation by deploying SPF, DKIM, and DMARC. These three email authentication protocols ensure messages sent from unauthorized entities don’t reach the recipients’ inboxes; such messages are either rejected or marked as spam.
Fake Seasonal Gigs
Be careful about job scams during the holidays when people are looking for extra work. Watch out for fake job ads, especially online ones that promise much money for very little work. **Don’t pay any money upfront for equipment or training for a new job. Also, don’t give out your personal info (like your social security number) or bank details unless you’re sure the job is real.
Be extra cautious about schemes where a fake boss asks you to cash a check, keep some money, and send the rest back.
Indulge in Safe Practices; Not Everything Red is Santa, Sometimes These Are Loud Red Flags
Always think before you click. There needs to be more than skimming the information: carefully read the details and look for unprofessional language and unusual terms and conditions. Yes, you can reach out to your bank to report fraud, but it comes at a cost. Your account freezes until the investigation is done, and the money is reversed in 30 to 60 days . So, being attentive seems like a better option.
Also, if you are a sexagenarian and above, you need to be **extra vigilant as hackers tend to target people of this age group due to their lack of proficiency with the latest technology.
We also suggest you **use credit cards over debit cards for shopping as they offer better protection against fraudulent activities.
Lastly, focus on email headers. Having different “From” and “Reply-To” email addresses in an email can sometimes be a red flag, as it might indicate an attempt to deceive or manipulate the recipient. In legitimate emails, the “From” and “Reply-To” addresses typically match to ensure that when a recipient replies to the email, the response goes back to the correct sender.
Scammers or phishing attempts may use different “From” and “Reply-To” addresses to trick recipients. For example, the “From” address may appear trustworthy, such as a well-known company or service, while the “Reply-To” address directs replies to a different, potentially malicious email address.
_However, it’s essential to note that not all cases of differing “From” and “Reply-To” addresses are maliciou_s. Some legitimate services and newsletters may use a different “Reply-To” address to manage responses effectively. Therefore, while it can be a potential red flag, it’s crucial to consider other factors, such as the content of the email, the sender’s reputation, and the presence of any suspicious links or requests, to assess the email’s legitimacy.
For more discussions and deployment of email-based cybersecurity, please reach out to us.
Topics

Content Specialist
Content Specialist at DMARC Report. Writes vendor-specific email authentication guides and troubleshooting walkthroughs.
LinkedIn Profile →Take control of your DMARC reports
Turn raw XML into actionable dashboards. Start free - no credit card required.