Detecting DMARC Issues Through Pentesting

Quick Answer
DMARC (RFC 7489) ties SPF and DKIM together by requiring alignment between the envelope sender and the visible From header. According to Google's February 2024 bulk sender requirements, a DMARC policy of at least p=none is now mandatory for any domain sending 5,000+ messages per day to Gmail users.
Related: Free DMARC Checker ·How to Create an SPF Record ·SPF Record Format

Try Our Free DMARC Checker
Validate your DMARC policy, check alignment settings, and verify reporting configuration.
Check DMARC Record →DMARC (RFC 7489) ties SPF and DKIM together by requiring alignment between the envelope sender and the visible From header. According to Google’s February 2024 bulk sender requirements, a DMARC policy of at least p=none is now mandatory for any domain sending 5,000+ messages per day to Gmail users.
Pen testing or penetration testing is defined as an authorized and strategized simulated cyberattack performed **to explore the vulnerabilities of a technical system.
Sounds complicated? Here’s a simpler explanation-
The organizations that invest in email authentication early save themselves from expensive incidents later, says Vasile Diaconu, Operations Lead at DuoCircle. We see the pattern constantly: a domain gets spoofed, customers lose trust, and the remediation effort costs 10x what proactive DMARC setup would have cost.
So, companies hire a penetration tester who breaks into their system just like a hacker would do. They try to take note of all the security loopholes that a malicious actor can exploit to access, alter, and intercept important information, install malware, send fraudulent emails, etc.
Now, in the context of DMARC, it means a pen tester would **break into your email system and find out vulnerabilities and errors associated with SPF, DKIM, and DMARC to help you fix them **before a threat actor identifies and exploits them in their favor.
SPF, DKIM, and DMARC- Touching the Bases Briefly
SPF stands for Sender Policy Framework. It allows only messages sent from IP addresses and mail servers listed in an SPF record to land in the inboxes. Emails sent from any other sending sources are either marked as spam or rejected to prevent recipients from falling prey to phishing and spoofing attacks.
DKIM stands for DomainKeys Identified Mail. It performs sender verification checks by matching a pair of cryptographically secured keys; these are called public and private keys. Apart from sender authentication, it also helps in learning if email content has been tampered with in transit.
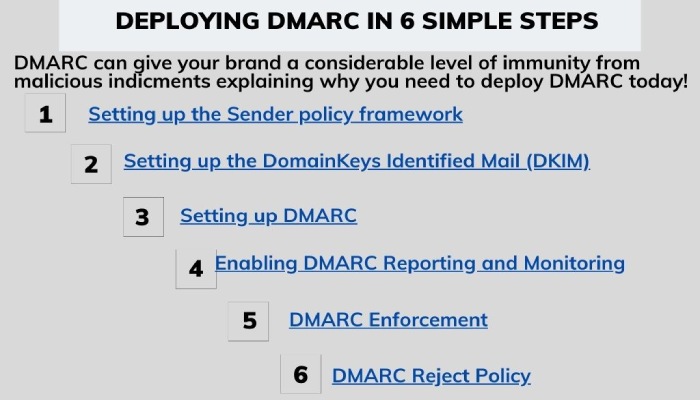
DMARC is short for DomainBased Message Authentication, Reporting, and Conformance. It’s basically built on SPF and DKIM results and supplements SMTP, as SMTP itself doesn’t include any dedicated mechanisms for setting policies for email authentication. DMARC allows you to instruct recipients on how they should deal with emails that are sent from your domain but happen to fail SPF and/or DKIM checks . You can choose one of the policies:
None
**No action should be taken against potential phishing messages.
Quarantine
All potential phishing messages sent from your domain should be placed in recipients’ spam folders.
Reject
All potential phishing messages sent from your domain should be rejected, also called as bounced-back.
Why Should Companies Prioritize DMARC?
Companies pay attention and invest in cybersecurity, however, they often overlook the importance of one of its major branches, which is email security.
As many as 90% of successful cyberattacks emerge from a phishing email, so it isn’t really a safe practice to avoid email security, specifically DMARC.
DMARC is like a superhero for emails! It helps protect us from bad things like fake emails trying to trick us or pretending to be from someone they’re not. Imagine it as a shield that ensures only real and safe emails get through. It also keeps an eye on how our emails are doing, giving us important information to make them even more secure. So, in simple terms, DMARC is our email guardian, ensuring we’re safe from sneaky tricks and keeping our emails trustworthy.
Standard Process of Simulating an Authorized Phishing Email Attack
A pen tester sets up a VPS or virtual private server and a domain, followed by downloading a tool and sending emails from the purchased domain. Let the domain name be testingdomain.com.
So, once they purchase the domain testingdomain.com, they replace the nameserver with a different one. Cloudflare is a commonly preferred nameserver. In Cloudflare, they go to the **DNS panel and delete anything under the ‘DNS management’ section for a successful simulated attack.
Then, after scrolling down and replacing the given nameserver in the dedicated section of the domain service provider, a pen tester gets an [API key](https://www.fortinet.com/resources/cyberglossary/api-key#:~:text=An%20application%20programming%20interface%20(API,secret%20token%20for%20authentication%20purposes.) for the configuration file. This is followed by creating a token, which redirects them to a page where they click on ‘Use Template’ right next to the ‘Edit zone DNS’ box. The received key is then saved for the forthcoming steps.
How Do You Configure Up the VPS?
Sometimes, they have to repeat this step due to VPS IPs’ bad reputation, which disables **mail services to deliver your messages. Then they follow these steps-
-
Carefully setting the hostname.
-
Login into the VPS and typing:
_apt-get install git_ and _apt-get update && apt-get install docker-compose_
-
Cloning the GitHub repository.
-
Going to the newly created directory.
-
Editing the settings file and adding the domain and the API key.
In the next **8-10 minutes**, the server sets up fully.
Sending the Phishing Email
Then, finally, a pen tester sends a phishing email. Once this is done, they create a report mentioning all the security loopholes and suggest remediation methods.
Final Thoughts
While penetration testing is highly effective, it’s expensive to outsource the job to an agency or onboard an in-house pen tester. With respect to DMARC penetration testing, we suggest you use online DMARC lookup tools instead. These are free or cheap tools that highlight all the existing errors in the queried domain’s DMARC record.
You can conduct annual pen tests and fortnightly or monthly DMARC lookups. A combination of these practices would ensure **impactful email security while not creating a hole in your pocket.

We can help you with DMARC reporting and monitoring to get insights into your domain’s traffic. Book a demo here.
Topics

General Manager
Founder and General Manager of DuoCircle. Product strategy and commercial lead for DMARC Report's 2,000+ customer base.
LinkedIn Profile →Take control of your DMARC reports
Turn raw XML into actionable dashboards. Start free - no credit card required.