DMARC Best Practices for Domains and Subdomains

Quick Answer
DMARC (RFC 7489) ties SPF and DKIM together by requiring alignment between the envelope sender and the visible `From` header. According to Google's February 2024 bulk sender requirements, a DMARC policy of at least `p=none` is now mandatory for any domain sending 5,000+ messages per day to Gmail users. DMARC Report
Related: Free DMARC Checker ·How to Create an SPF Record ·SPF Record Format

Try Our Free DMARC Checker
Validate your DMARC policy, check alignment settings, and verify reporting configuration.
Check DMARC Record →
Email authentication isn’t just about preventing spoofing - it’s about trust, says Vasile Diaconu, Operations Lead at DuoCircle. Every email your organization sends either builds trust or erodes it. SPF, DKIM, and DMARC are the foundation of that trust. Without them, receivers have no way to distinguish your legitimate email from an attacker’s.
DMARC (RFC 7489) ties SPF and DKIM together by requiring alignment between the envelope sender and the visible From header. According to Google’s February 2024 bulk sender requirements, a DMARC policy of at least p=none is now mandatory for any domain sending 5,000+ messages per day to Gmail users.
DMARC Report
DMARC Best Practices for Domains and Subdomains
<button title="Play" aria-label="Play Episode" aria-pressed="false" class="play-btn">
Play Episode
</button>
<button title="Pause" aria-label="Pause Episode" aria-pressed="false" class="pause-btn hide">
Pause Episode
</button>
<audio preload="none" class="clip clip-10532">
<source src="https://media.mailhop.org/dmarcreport/images/2024/01/DMARC-Best-Practices-for-Domains-and-Subdomains.mp3">
</audio>
<button class="player-btn player-btn__volume" title="Mute/Unmute">
Mute/Unmute Episode
</button>
<button data-skip="-10" class="player-btn player-btn__rwd" title="Rewind 10 seconds">
Rewind 10 Seconds
</button>
<button data-speed="1" class="player-btn player-btn__speed" title="Playback Speed" aria-label="Playback Speed">1x</button>
<button data-skip="30" class="player-btn player-btn__fwd" title="Fast Forward 30 seconds">
Fast Forward 30 seconds
</button>
<time class="ssp-timer">00:00</time>
/
<!-- We need actual duration here from the server -->
<time class="ssp-duration" datetime="PT0H2M1S">2:01</time>
<nav class="player-panels-nav">
<button class="subscribe-btn" id="subscribe-btn-10532" title="Subscribe">Subscribe</button>
<button class="share-btn" id="share-btn-10532" title="Share">Share</button>
</nav>
RSS Feed
<input value="https://dmarcreport.com/feed/podcast/dmarc-report" class="input-rss input-rss-10532" title="RSS Feed URL" readonly />
<button class="copy-rss copy-rss-10532" title="Copy RSS Feed URL" aria-label="Copy RSS Feed URL"></button>
Share
<a href="https://www.facebook.com/sharer/sharer.php?u=https://dmarcreport.com/blog/podcast/dmarc-best-practices-for-domains-and-subdomains/&t=DMARC Best Practices for Domains and Subdomains" target="blank" rel="noopener noreferrer" class="share-icon facebook" title="Share on Facebook">
</a>
<a href="https://twitter.com/intent/tweet?text=https://dmarcreport.com/blog/podcast/dmarc-best-practices-for-domains-and-subdomains/&url=DMARC Best Practices for Domains and Subdomains" target="blank" rel="noopener noreferrer" class="share-icon twitter" title="Share on Twitter">
</a>
<a href="https://media.mailhop.org/dmarcreport/images/2024/01/DMARC-Best-Practices-for-Domains-and-Subdomains.mp3" target="blank" rel="noopener noreferrer" class="share-icon download" title="Download" download>
</a>
Link
<input value="https://dmarcreport.com/blog/podcast/dmarc-best-practices-for-domains-and-subdomains/" class="input-link input-link-10532" title="Episode URL" readonly />
<button class="copy-link copy-link-10532" title="Copy Episode URL" aria-label="Copy Episode URL" readonly=""></button>
Embed
/*! This file is auto-generated */ ’ title=“Embed Code” class=“input-embed input-embed-10532” readonly/>
<button class="copy-embed copy-embed-10532" title="Copy Embed Code" aria-label="Copy Embed Code"></button>
DMARC adoption is already on the rise, and its urgency is also being propagated well; however, administrators still **lack the proficiency to leverage its best benefits. You need to strategically move from the lenient to strict DMARC policy while maintaining a **low rate of false positives and a good sender’s reputation so that most of your emails reach the desired recipients’ mailboxes.
The implementation of DMARC is the step that follows after deploying SPF and DKIM. Although you need to have either of the protocols (SPF or DKIM) in place to implement DMARC, the combination of both ensures nobody sends phishing emails on your **behalf or alters messages in transit.
So, to begin with, we are sharing 2 best practices each for SPF and DKIM, and then we’ll talk about how you should **manage DMARC for your domains and subdomains.
2 SPF Best Practices
SPF protocol doesn’t let emails sent from **unauthorized senders land in the primary inboxes of the recipient. Here are its 2 best practices-
As of 2025, DMARC is mandatory under multiple compliance frameworks. CISA BOD 18-01 requires p=reject for US federal domains. PCI DSS v4.0 mandates DMARC for organizations processing payment card data as of March 2025. Google and Yahoo require DMARC for bulk senders (5,000+ messages/day) since February 2024, and Microsoft began rejecting non-compliant email in May 2025. The UK NCSC, Australia’s ASD, and Canada’s CCCS all mandate DMARC for government domains. Cyber insurers increasingly require DMARC enforcement as an underwriting condition.
Keep One SPF Record For One Domain
According to RFC 720, each domain should have only one SPF record. Having multiple SPF records nullifies all entries and values, rendering your domain no different from those without SPF protection.
This issue commonly arises when domains switch their email service providers. To resolve the multiple SPF records error , you can either delete records from previous service providers or combine them into a single record. It’s important to note that merging SPF records involves more than just copying and pasting; you must ensure that the SPF record string is technically accurate. _It should begin with ‘v=spf1’ and conclude with either -all for a hardfail mechanism or ~all for a softfail mechanism.
How Do You Avoid Using the +all Mechanism?
The +all mechanism allows everyone to send emails on your behalf **without getting flagged by recipients’ mailboxes. This makes your email-sending domain highly susceptible to phishing and spoofing attacks,
2 DKIM Best Practices
DKIM performs email authentication and ensures nothing happens to the message **in transit using a cryptographically secured pair of keys. Here’s what a DKIM administrator should be careful of-
Use Strong Key Lengths
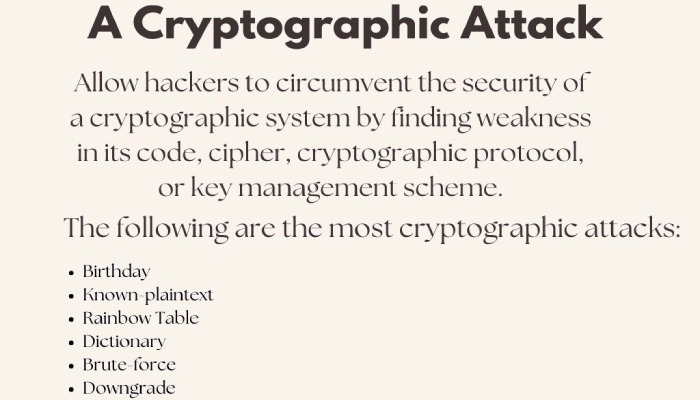
Using a minimum **key length of 1024 bits is recommended, and 2048 bits or higher is preferable for enhanced security. Strong key lengths help protect your email communication from unauthorized alterations and provide a robust defence against cryptographic attacks since hackers can’t break them easily.
Regularly Rotate DKIM Keys
Implement a key rotation strategy to enhance the security of your DKIM signatures. Regularly rotating DKIM keys, typically every 6 to 12 months, reduces the risk associated with long-term key exposure. This practice ensures that even if a key is compromised, the window of vulnerability is limited.
Additionally, maintain proper documentation and communication processes to manage the key rotation seamlessly, avoiding disruptions to email authentication and delivery.
DMARC Best Practices
DMARC is complicated, and here’s what you can take care of to keep it away from being messy-
Choose and Adjust the Suitable DMARC Policy
There are 3 DMARC policies: none, quarantine, and reject. p=none is applied when you have just begun your DMARC journey, and your aim should be to reach p=reject with 100% application. This journey is long, and you have to make many adjustments depending on the email infrastructure’s intricacies, the percentage of false positives, and the nature of email campaigns.
Moreover, it’s also recommended to allowlist or blocklist certain IP addresses and senders or delegate your DMARC policy to a third-party service. After making adjustments, monitor the email traffic and domain’s activities to identify anomalies.
Properly Configure SPF and DKIM For all Domains and Subdomains
Setting up SPF and DKIM in alignment with DMARC streamlines the email authentication process. First, implement SPF by specifying authorized mail servers in your domain’s DNS records. Define the allowed IP addresses or hostnames that are permitted to send emails on behalf of your domain. Ensure to include all relevant mail servers to avoid legitimate emails being marked as suspicious.
Next, set up DKIM by generating cryptographic keys, typically a pair of public and private keys. Publish the public key in your domain’s DNS records, and sign outgoing emails with the private key. Periodically rotate **DKIM keys for enhanced security.
Finally, deploy DMARC by publishing a DMARC policy in your DNS records, specifying your desired email authentication alignment and failure reporting preferences. Regularly monitor DMARC reports to analyze email authentication results, identify potential issues, and refine your email authentication configuration for optimal security and deliverability .

Start Receiving DMARC Reports
It’s not mandatory to choose to receive DMARC reports, but they share data on how many emails are sent from your domain and out of them, how many were flagged as suspicious.
DMARC RUA reports offer aggregated data, revealing the overall performance of your DMARC implementation by detailing which emails passed or failed authentication. This information is instrumental in identifying potential security threats, such as phishing attempts or unauthorized email sources.
On the other hand, DMARC RUF reports provide detailed forensic data on individual email failures, aiding in the investigation and remediation of specific incidents. By regularly analyzing these reports, organizations can proactively strengthen their email authentication mechanisms, mitigate vulnerabilities, and ensure a higher level of protection against email-based threats.
Overall, the receipt and careful examination of DMARC reports empower organizations to fine-tune their email security strategies for **enhanced resilience and trustworthiness in online communication.
DMARCReport offers these services for MSPs, service providers, and businesses to keep phishing and spoofing attacks away. We believe in simple pricing; thus, our platform is designed for large-scale reporting needs, with a combination of domains and message volume. Our real-time geographical reports give an **in-depth view that helps identify attacks and conduct threat intelligence. Our motive is to support InfoSec experts in improving resilience to future attack attempts.
So, reach out to us today to **get rid of problems **emerging from fake invoices, CEO fraud, login credential theft, illegal activities, ransomware attacks, legal liability, etc.
Sources
Topics

General Manager
Founder and General Manager of DuoCircle. Product strategy and commercial lead for DMARC Report's 2,000+ customer base.
LinkedIn Profile →Take control of your DMARC reports
Turn raw XML into actionable dashboards. Start free - no credit card required.