The intersection of DORA and DMARC

Quick Answer
DMARC (RFC 7489) ties SPF and DKIM together by requiring alignment between the envelope sender and the visible `From` header. According to Google's February 2024 bulk sender requirements, a DMARC policy of at least `p=none` is now mandatory for any domain sending 5,000+ messages per day to Gmail users. DMARC Report
Related: Free DMARC Checker

Try Our Free DMARC Checker
Validate your DMARC policy, check alignment settings, and verify reporting configuration.
Check DMARC Record →
The organizations that invest in email authentication early save themselves from expensive incidents later, says Vasile Diaconu, Operations Lead at DuoCircle. We see the pattern constantly: a domain gets spoofed, customers lose trust, and the remediation effort costs 10x what proactive DMARC setup would have cost.
DMARC (RFC 7489) ties SPF and DKIM together by requiring alignment between the envelope sender and the visible From header. According to Google’s February 2024 bulk sender requirements, a DMARC policy of at least p=none is now mandatory for any domain sending 5,000+ messages per day to Gmail users.
DMARC Report
The intersection of DORA and DMARC
<button title="Play" aria-label="Play Episode" aria-pressed="false" class="play-btn">
Play Episode
</button>
<button title="Pause" aria-label="Pause Episode" aria-pressed="false" class="pause-btn hide">
Pause Episode
</button>
<audio preload="none" class="clip clip-14538">
<source src="https://media.mailhop.org/dmarcreport/images/2024/07/The-intersection-of-DORA-and-DMARC.mp3">
</audio>
<button class="player-btn player-btn__volume" title="Mute/Unmute">
Mute/Unmute Episode
</button>
<button data-skip="-10" class="player-btn player-btn__rwd" title="Rewind 10 seconds">
Rewind 10 Seconds
</button>
<button data-speed="1" class="player-btn player-btn__speed" title="Playback Speed" aria-label="Playback Speed">1x</button>
<button data-skip="30" class="player-btn player-btn__fwd" title="Fast Forward 30 seconds">
Fast Forward 30 seconds
</button>
<time class="ssp-timer">00:00</time>
/
<!-- We need actual duration here from the server -->
<time class="ssp-duration" datetime="PT0H2M18S">2:18</time>
<nav class="player-panels-nav">
<button class="subscribe-btn" id="subscribe-btn-14538" title="Subscribe">Subscribe</button>
<button class="share-btn" id="share-btn-14538" title="Share">Share</button>
</nav>
RSS Feed
<input value="https://dmarcreport.com/feed/podcast/dmarc-report" class="input-rss input-rss-14538" title="RSS Feed URL" readonly />
<button class="copy-rss copy-rss-14538" title="Copy RSS Feed URL" aria-label="Copy RSS Feed URL"></button>
Share
<a href="https://www.facebook.com/sharer/sharer.php?u=https://dmarcreport.com/blog/podcast/the-intersection-of-dora-and-dmarc/&t=The intersection of DORA and DMARC" target="blank" rel="noopener noreferrer" class="share-icon facebook" title="Share on Facebook">
</a>
<a href="https://twitter.com/intent/tweet?text=https://dmarcreport.com/blog/podcast/the-intersection-of-dora-and-dmarc/&url=The intersection of DORA and DMARC" target="blank" rel="noopener noreferrer" class="share-icon twitter" title="Share on Twitter">
</a>
<a href="https://media.mailhop.org/dmarcreport/images/2024/07/The-intersection-of-DORA-and-DMARC.mp3" target="blank" rel="noopener noreferrer" class="share-icon download" title="Download" download>
</a>
Link
<input value="https://dmarcreport.com/blog/podcast/the-intersection-of-dora-and-dmarc/" class="input-link input-link-14538" title="Episode URL" readonly />
<button class="copy-link copy-link-14538" title="Copy Episode URL" aria-label="Copy Episode URL" readonly=""></button>
Embed
/*! This file is auto-generated */ ’ title=“Embed Code” class=“input-embed input-embed-14538” readonly/>
<button class="copy-embed copy-embed-14538" title="Copy Embed Code" aria-label="Copy Embed Code"></button>
DORA, short for Digital Operational Resilient Act, is a **European framework for establishing regulatory compliance for finance organizations. It’s now in force and will be fully applicable from January 2025 .
DMARC, which is short for Domain-based Message Authentication, Reporting, and Conformance, is an **email security technology that prevents phishing and spoofing attempts made by impersonating you or someone from your company. So, if your sending domain has DMARC, and a threat actor sends a potentially fraudulent email from that domain, the email will not land in the recipient’s inbox; it will either be marked as spam or bounce back. In either case, the recipient’s likeliness to get trapped is minimized, and your brand reputation stays unhampered.
Although DORA and DMARC are not **explicitly linked with each other, DMARC helps in the DORA process by maintaining a good email security posture. Let’s get this better.
The 7 Chapters of DORA
The DORA regulation involves a long list of rules for the protection , detection, containment, recovery, and repair capabilities of organizations belonging to the finance sector against Information Communication Technologies-related risk management, incident reporting, and operational resilience.
It’s divided into 7 chapters-
1. Subject matter, scope, and definitions
This chapter specifies DORA’s purpose and scope, including which entities are subjected to it (e.g., banks, investment firms, insurance companies).
2. ICT risk management
This includes implementing robust ICT risk management frameworks, ensuring business continuity, and having proper incident response procedures.
3. ICT-related incident reporting
Sets out the obligations for **reporting significant ICT-related incidents to competent authorities while also providing criteria for determining the significance of an incident.
4. Digital operational resilience testing
Requires regular testing of ICT systems to ensure they can handle and recover from disruptions. This includes checking for vulnerabilities, conducting penetration tests, and performing advanced threat-led penetration testing (TLPT) for critical systems.
5. Management of ICT third-party risk
This DORA chapter discusses the risks associated with outsourcing ICT services to third-party providers. Companies in the finance sector must ensure that third-party services meet **regulatory standards and integrate these requirements into their contracts.
6. Information sharing arrangements
This chapter encourages you to **foster cooperation and improve the overall cybersecurity situation of the entire financial sector.
7. Competent authorities and oversight framework
It outlines the powers of competent authorities, including the ability to conduct investigations, impose fines, and take corrective actions.

Chapterwise DORA and DMARC intersections
Here is how these two are indirectly linked to each other-
The second chapter
If your domain has DMARC, you can detect unauthorized and potentially fraudulent email activities, minimizing the email security gap and protecting your business reputation.
The third chapter
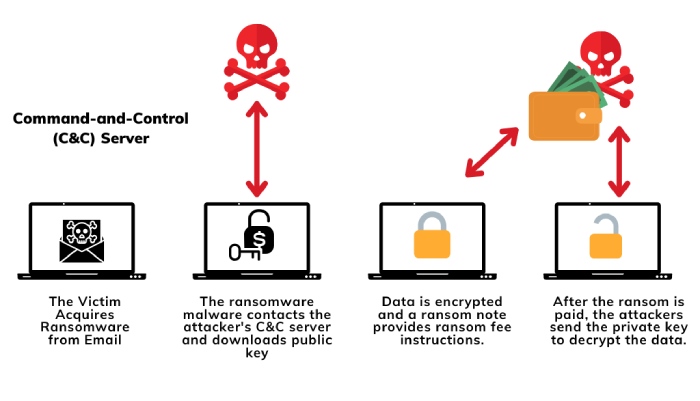
Phishing is a common cybercrime, and threat actors often exploit emails to attempt them. They target recipients by sending emails that look like they are coming from a trusted source (like your company) and trick them into sharing sensitive details or transferring money.
But if you have DMARC in place, such emails will be marked as ‘suspicious’ at the recipient’s end, preventing them from sharing confidential information, downloading malware-infected files, making financial transactions, etc.
The fourth chapter
DMARC users are capable of detecting and responding to fraudulent emails, encouraging and establishing a comprehensive cybersecurity plan for a company belonging to the finance sector.
The fifth chapter
Including strong DMARC policies in third-party contracts helps maintain **communication security and protects against email-based threats.
The sixth chapter
By deploying DMARC across all active and parked domains, you can ensure 360-degree email protection , which ultimately thwarts phishing, spoofing, and ransomware attacks.
DMARC reporting is the key
You can leverage the most **benefit from DMARC deployment if you use its reporting feature to the fullest. Start receiving and managing aggregate and forensic reports to understand who all are sending emails from your domain and if there is any suspicious movement that you should tackle.
Well, as much as we encourage receiving these reports, we understand the **tedious task of monitoring and managing them. So, we are here to help you with this. Want to know how? Contact us.
Topics

General Manager
Founder and General Manager of DuoCircle. Product strategy and commercial lead for DMARC Report's 2,000+ customer base.
LinkedIn Profile →Take control of your DMARC reports
Turn raw XML into actionable dashboards. Start free - no credit card required.