A Roundup of the Top Phishing Attacks in 2024 So Far

Quick Answer
_According to the FBI's 2022 Internet Crime Report (IC3), 300,497 US-based victims reported phishing incidents in a single year, and Business Email Compromise (BEC) caused more than $2.7 billion in direct losses. DMARC Report A Roundup of the Top Phishing Attacks in 2024 So Far
Related: Free DMARC Checker ·How to Create an SPF Record ·SPF Record Format


Domain spoofing is trivially easy without DMARC enforcement, says Brad Slavin, General Manager of DuoCircle. Anyone can send email that looks like it comes from your domain. DMARC with p=reject is the only way to tell receiving servers to block unauthorized senders completely.
_According to the FBI’s 2022 Internet Crime Report (IC3), 300,497 US-based victims reported phishing incidents in a single year, and Business Email Compromise (BEC) caused more than $2.7 billion in direct losses. DMARC Report
A Roundup of the Top Phishing Attacks in 2024 So Far
<button title="Play" aria-label="Play Episode" aria-pressed="false" class="play-btn">
Play Episode
</button>
<button title="Pause" aria-label="Pause Episode" aria-pressed="false" class="pause-btn hide">
Pause Episode
</button>
<audio preload="none" class="clip clip-13147">
<source src="https://media.mailhop.org/dmarcreport/images/2024/05/A-Roundup-of-the-Top-Phishing-Attacks-in-2024-So-Far.mp3">
</audio>
<button class="player-btn player-btn__volume" title="Mute/Unmute">
Mute/Unmute Episode
</button>
<button data-skip="-10" class="player-btn player-btn__rwd" title="Rewind 10 seconds">
Rewind 10 Seconds
</button>
<button data-speed="1" class="player-btn player-btn__speed" title="Playback Speed" aria-label="Playback Speed">1x</button>
<button data-skip="30" class="player-btn player-btn__fwd" title="Fast Forward 30 seconds">
Fast Forward 30 seconds
</button>
<time class="ssp-timer">00:00</time>
/
<!-- We need actual duration here from the server -->
<time class="ssp-duration" datetime="PT0H2M12S">2:12</time>
<nav class="player-panels-nav">
<button class="subscribe-btn" id="subscribe-btn-13147" title="Subscribe">Subscribe</button>
<button class="share-btn" id="share-btn-13147" title="Share">Share</button>
</nav>
RSS Feed
<input value="https://dmarcreport.com/feed/podcast/dmarc-report" class="input-rss input-rss-13147" title="RSS Feed URL" readonly />
<button class="copy-rss copy-rss-13147" title="Copy RSS Feed URL" aria-label="Copy RSS Feed URL"></button>
Share
<a href="https://www.facebook.com/sharer/sharer.php?u=https://dmarcreport.com/blog/podcast/a-roundup-of-the-top-phishing-attacks-in-2024-so-far/&t=A Roundup of the Top Phishing Attacks in 2024 So Far" target="blank" rel="noopener noreferrer" class="share-icon facebook" title="Share on Facebook">
</a>
<a href="https://twitter.com/intent/tweet?text=https://dmarcreport.com/blog/podcast/a-roundup-of-the-top-phishing-attacks-in-2024-so-far/&url=A Roundup of the Top Phishing Attacks in 2024 So Far" target="blank" rel="noopener noreferrer" class="share-icon twitter" title="Share on Twitter">
</a>
<a href="https://media.mailhop.org/dmarcreport/images/2024/05/A-Roundup-of-the-Top-Phishing-Attacks-in-2024-So-Far.mp3" target="blank" rel="noopener noreferrer" class="share-icon download" title="Download" download>
</a>
Link
<input value="https://dmarcreport.com/blog/podcast/a-roundup-of-the-top-phishing-attacks-in-2024-so-far/" class="input-link input-link-13147" title="Episode URL" readonly />
<button class="copy-link copy-link-13147" title="Copy Episode URL" aria-label="Copy Episode URL" readonly=""></button>
Embed
/*! This file is auto-generated */ ’ title=“Embed Code” class=“input-embed input-embed-13147” readonly/>
<button class="copy-embed copy-embed-13147" title="Copy Embed Code" aria-label="Copy Embed Code"></button>
Is your mailbox flooded with unsolicited emails? While most of these emails are harmless (like bulk or spam), some of them have the potential to seriously damage your entire ecosystem. Year after year, these emails are getting more frequent and formidable. In fact, we are only halfway into 2024, and the number of fraudulent emails that make it into the targets’ inboxes continues to surge.
A recent report by SlashNext revealed a 341% increase in malicious emails, and **AI has substantially contributed to this number.
Let us take a look at some of the most **notable phishing attacks that we witnessed in 2024.
Notable Phishing Attacks of 2024
Undoubtedly, we have come a long way in terms of technological advancements , but with this progress, the like phishing has also evolved, which certainly is not in our favor. With each passing year, cybercriminals are getting smarter at employing new techniques, evading security measures, and infiltrating the systems of their targets, and the year 2024 is a testament to this.
While there are many ways for cyber attackers to access private corners of your digital ecosystem, email remains the most preferred attack vector.
Here are some of the most severe email-based phishing attacks of 2024 that you should know about:
Microsoft and Google Phishing Attacks
A recent report by Check Point unveiled that Microsoft and Google are the major brands susceptible to being spoofed to execute phishing attacks. In the first quarter of 2024, Microsoft accounted for 38% of all attempted brand phishing attempts, making it the top target, followed by Google at 11%. What’s more interesting is that most of these attacks typically involved seemingly legitimate emails, meticulously crafted to trick recipients into providing their login credentials or other sensitive information.
Pepco Social Engineering Attack
Apart from tech giants, threat actors continue to target retail businesses in 2024. One such incident happened in February 2024, when Pepco Group, a major European retailer, lost around €15.5 million in a devastating attack. According to the COO of OSP Cyber Academy , Irene Coyle, the incident was likely a phishing attack that involved fraudsters spoofing legitimate employee emails to deceive the finance staff into transferring funds.
Although there isn’t much clarity on the specifics of the technique, it is speculated that the attack was executed by employing state-of-the-art AI tools that made it **difficult for the victims to see through the deceit and prevent themselves from falling prey.
Malware Disguised as a Bank Payment Notice
In March 2024, a new phishing campaign emerged that used a novel loader malware to deliver Agent Tesla, which plays the role of an information stealer and keylogger. This attack was uncovered by Trustwave SpiderLabs, which identified that the attack chain began with a **phishing email masquerading as a bank payment notice. The message was so well crafted that it successfully compelled the users to open an archive file attachment.
This seemingly benign attachment concealed the malicious loader, which used obfuscation techniques to evade detection, bypass antivirus defenses, and deploy Agent Tesla to **steal sensitive data from the affected server.
StrelaStealer Phishing Attacks
Recently, a new wave of phishing attacks has come to the surface that has affected over 100 organizations across the European Union and the United States. According to the researchers at Palo Alto Networks’ Unit 42, these attacks stem from **spam emails with attachments that deliver the StrelaStealer malware .
The approach behind this attack is so uncomplicated yet sophisticated that it escaped the purview of the employees of more than 100 companies. In an attempt to evade detection, the attackers simply changed the file format of the attachment and successfully managed to achieve their **malicious intentions of stealing email login data across sectors like finance, government, and manufacturing.
Learning From the Mistakes
With email being one of the most common channels of communication for the good, bad, and ugly, email-based phishing attacks are here to stay! But this does not mean you cannot protect your organization from succumbing to such attacks.
Follow these tips to **mitigate the risk of email-based phishing attacks and strengthen your security posture.
How Do You Implement Multi-Factor Authentication (MFA)?
Gone are the days of single-factor authentication. As email ecosystems and attacks targeting these ecosystems become more complex, it is clear that we need a solution that offers comprehensive and layered protection. Multi-factor authentication (MFA), like a two-step verification process, checks these boxes and makes it significantly harder for attackers to gain unauthorized access.
How Do You Maintain Your Software Regularly?
An often-overlooked way to prevent phishing attacks is to ensure that all software, including email clients and security tools, are kept up to date. This simple step can help you identify and patch any **new or existing vulnerabilities that attackers could potentially exploit.
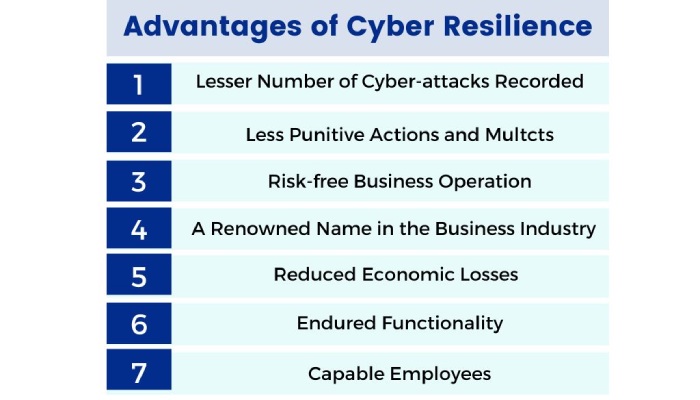
Conduct Employee Training
It is important that your employees recognize and understand the threats looming over the digital landscape, the latest tactics used in phishing attacks, and more. Regular training sessions among your teams can prove to be a big leap toward cultivating a culture of cyber resilience. The sessions should cover everything about email-based phishing attacks - how to identify suspicious emails, links, and attachments, how to respond to them, and most importantly, how to report them.
Prioritize Email Authentication
Implementing email authentication protocols (SPF, DKIM, and DMARC) is a robust and non-negotiable approach to minimizing the risks of email phishing attacks. By properly configuring these protocols, you can ensure that incoming emails are validated, thereby reducing the risks of phishing attacks, spoofed emails, and email impersonation.
To Sum Up
Now that you are aware of the most notable phishing attacks of 2024, it is crucial to strategically leverage this information to adopt a proactive approach to cybersecurity.
While this might seem like a complex endeavor, you can **trust our team at DMARCReport to solve your email authentication woes.
Need help? Reach out to us today to safeguard your organization’s digital assets!
Topics

Operations Lead
Operations Lead at DuoCircle. Runs project management, developer coordination, and technical support execution for DMARC Report.
LinkedIn Profile →Take control of your DMARC reports
Turn raw XML into actionable dashboards. Start free - no credit card required.