DMARC Adoption Amongst UK Banks

Quick Answer
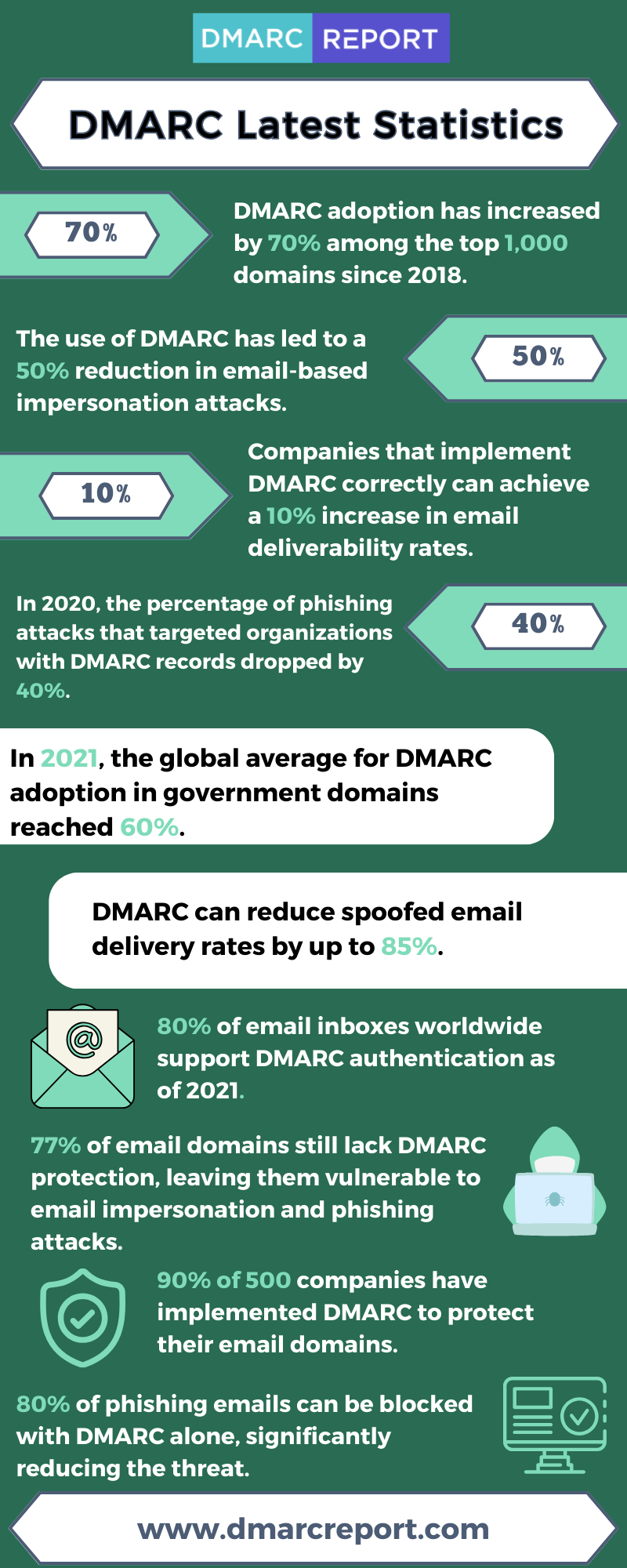
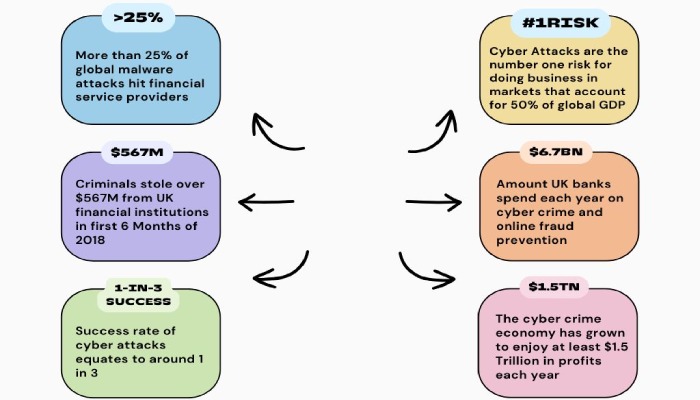
DMARC is an essential tool for enhancing [email security](https://dmarcreport.com/blog/why-email-security-matters-and-how-to-get-it-right/), especially within the financial sector. Financial institutions are a prime target for cybercriminals, given the potentially lucrative rewards associated with fraudulent transactions. Phishing attacks targeting the financial sector, encompassing banks among other institutions, continued to dominate as the most prevalent type of cyberattack, constituting a substantial [23.6 per cent](https://docs.apwg.org/reports/apwgtrendsreportq12021.pdf) of all phishing incidents.
Related: Free DMARC Checker

Try Our Free DMARC Checker
Validate your DMARC policy, check alignment settings, and verify reporting configuration.
Check DMARC Record →DMARC is an essential tool for enhancing email security, especially within the financial sector. _Financial institutions are a prime target for cybercriminals, given the potentially lucrative rewards associated with _fraudulent transactions. Phishing attacks targeting the financial sector, encompassing banks among other institutions, continued to dominate as the most prevalent type of cyberattack, constituting a substantial 23.6 per cent of all phishing incidents.
The organizations that invest in email authentication early save themselves from expensive incidents later, says Vasile Diaconu, Operations Lead at DuoCircle. We see the pattern constantly: a domain gets spoofed, customers lose trust, and the remediation effort costs 10x what proactive DMARC setup would have cost.
DMARC (RFC 7489) ties SPF and DKIM together by requiring alignment between the envelope sender and the visible From header. According to Google’s February 2024 bulk sender requirements, a DMARC policy of at least p=none is now mandatory for any domain sending 5,000+ messages per day to Gmail users.
However, despite the critical need for robust email security, the adoption of DMARC in the financial industry, particularly among UK banks, still lags behind.
According to data from a CIO Insight report, the adoption of DMARC in the financial services sector is at only 57 percent. This statistic is concerning, as it implies that a significant portion of financial institutions , including banks, may still be vulnerable to phishing attacks and email fraud.
The reasons for this slow adoption could vary. This may be due to the perception of **DMARC implementation as a complex and resource-intensive process . Some organizations may also be concerned about false positives or operational disruptions that can occur during the initial stages of DMARC deployment.
Decoding DMARC
DMARC (Domain-based Message Authentication, Reporting, and Conformance) is an **email authentication protocol that helps to protect domain owners and their customers from email spoofing and phishing attacks. DMARC builds on two other email authentication protocols, SPF and DKIM. SPF (Sender Policy Framework) verifies that an email is being sent from an authorized IP address, while DKIM (DomainKeys Identified Mail) verifies that the content of an email has not been tampered with.
DMARC allows domain owners to **publish a policy that tells receiving mail servers what to do with emails that fail SPF and/or DKIM authentication. The three possible policy options are:
Monitor (p=none) This is the default policy, and it tells email providers to
take no action if an email fails DMARC authentication. This policy is useful for monitoring the health of your email security posture, but it does not provide any protection against fraudulent emails.

Quarantine (p=quarantine)
This policy tells **email providers to move emails that fail DMARC authentication to a spam or junk folder. This policy provides some protection against fraudulent emails, but it is possible for some fraudulent emails to make it through to the recipient’s inbox.
Reject (p=reject)
This policy tells email providers to **reject emails that fail DMARC authentication. This policy provides the **highest level of protection against fraudulent emails, but it is important to note that some legitimate emails may also be rejected.
The level of protection that organizations choose when implementing DMARC depends on their specific needs and risk tolerance. Starting with the “monitor” policy is often recommended for those who are new to DMARC. This policy allows organizations to collect data and gain insights into their email security landscape **without immediately blocking any emails. It acts as a starting point to assess the effectiveness of their email authentication and identify potential issues.
_Once you have established a baseline for your email security posture, you can then consider moving to a more aggressive policy, such as quarantine or reject.
DMARC Adoption Amongst the UK Banks and Global Trend
Despite the clear benefits of adopting a “policy=reject” stance in DMARC implementation, as it significantly reduces the risk of fraudulent emails infiltrating your network, the reality is that many UK banks have yet to reach this level of email security: only less than half of UK banks implement policy=reject.
This presents a **glaring security gap in a sector where the stakes are exceptionally high, and proactive measures should be prioritized to safeguard financial transactions and customer trust.
When we look at the DMARC status of the top 100 global banks, the situation remains less than ideal but shows an optimistic trend nonetheless. One encouraging trend is the significant increase of 200% in DMARC policies set to the “p=quarantine” level. This indicates that an increasing number of these prominent financial institutions are taking proactive measures to enhance their email security. This approach allows organizations to take a more cautious stance while still preventing potentially harmful emails from reaching their recipients.
There’s an 18% decrease in the number of companies within this group that lack a DMARC policy altogether. This signifies a growing awareness within the financial sector about the importance of email authentication and the need to bolster defenses against phishing attacks and email fraud. Implementing a DMARC policy, even at the monitoring level, represents a significant step towards enhancing email security, as it enables organizations to gain insights into their email traffic and detect potential threats.
Conclusion
The global banking sector, which is entrusted with vast sums of money and sensitive customer information, should ideally be at the forefront of email security. However, the data suggests that there is still work to be done in achieving comprehensive DMARC adoption and implementation .
The consequences of **inadequate email security in the financial sector are severe. Phishing attacks and email fraud can result in substantial financial losses, damage to the reputation of financial institutions, and harm to customers. Regulatory bodies are increasingly emphasizing the need for robust email security, and DMARC compliance is often considered a best practice in this regard.
To find out more about how DMARC can safeguard you against cyber threats, get in touch.
Topics

General Manager
Founder and General Manager of DuoCircle. Product strategy and commercial lead for DMARC Report's 2,000+ customer base.
LinkedIn Profile →Take control of your DMARC reports
Turn raw XML into actionable dashboards. Start free - no credit card required.