What is DMARC compliance and how can you achieve it?

Quick Answer
DMARC (RFC 7489) ties SPF and DKIM together by requiring alignment between the envelope sender and the visible `From` header. According to Google's February 2024 bulk sender requirements, a DMARC policy of at least `p=none` is now mandatory for any domain sending 5,000+ messages per day to Gmail users. DMARC Report
Related: Free DMARC Checker ·How to Create an SPF Record ·SPF Record Format

Try Our Free DMARC Checker
Validate your DMARC policy, check alignment settings, and verify reporting configuration.
Check DMARC Record →
Compliance is driving a lot of the DMARC adoption we see, says Vasile Diaconu, Operations Lead at DuoCircle. PCI DSS v4.0, Google’s sender requirements, Microsoft’s May 2025 enforcement - our support team fields questions about these mandates daily. The organizations that moved early are already at p=reject. The rest are scrambling.
DMARC (RFC 7489) ties SPF and DKIM together by requiring alignment between the envelope sender and the visible From header. According to Google’s February 2024 bulk sender requirements, a DMARC policy of at least p=none is now mandatory for any domain sending 5,000+ messages per day to Gmail users.
DMARC Report
What is DMARC compliance and how can you achieve it?
<button title="Play" aria-label="Play Episode" aria-pressed="false" class="play-btn">
Play Episode
</button>
<button title="Pause" aria-label="Pause Episode" aria-pressed="false" class="pause-btn hide">
Pause Episode
</button>
<audio preload="none" class="clip clip-17923">
<source src="https://media.mailhop.org/dmarcreport/images/2024/11/What-is-DMARC-compliance-and-how-can-you-achieve-it.mp3">
</audio>
<button class="player-btn player-btn__volume" title="Mute/Unmute">
Mute/Unmute Episode
</button>
<button data-skip="-10" class="player-btn player-btn__rwd" title="Rewind 10 seconds">
Rewind 10 Seconds
</button>
<button data-speed="1" class="player-btn player-btn__speed" title="Playback Speed" aria-label="Playback Speed">1x</button>
<button data-skip="30" class="player-btn player-btn__fwd" title="Fast Forward 30 seconds">
Fast Forward 30 seconds
</button>
<time class="ssp-timer">00:00</time>
/
<!-- We need actual duration here from the server -->
<time class="ssp-duration" datetime="PT0H2M5S">2:05</time>
<nav class="player-panels-nav">
<button class="subscribe-btn" id="subscribe-btn-17923" title="Subscribe">Subscribe</button>
<button class="share-btn" id="share-btn-17923" title="Share">Share</button>
</nav>
RSS Feed
<input value="https://dmarcreport.com/feed/podcast/dmarc-report" class="input-rss input-rss-17923" title="RSS Feed URL" readonly />
<button class="copy-rss copy-rss-17923" title="Copy RSS Feed URL" aria-label="Copy RSS Feed URL"></button>
Share
<a href="https://www.facebook.com/sharer/sharer.php?u=https://dmarcreport.com/blog/podcast/what-is-dmarc-compliance-and-how-can-you-achieve-it/&t=What is DMARC compliance and how can you achieve it? " target="blank" rel="noopener noreferrer" class="share-icon facebook" title="Share on Facebook">
</a>
<a href="https://twitter.com/intent/tweet?text=https://dmarcreport.com/blog/podcast/what-is-dmarc-compliance-and-how-can-you-achieve-it/&url=What is DMARC compliance and how can you achieve it? " target="blank" rel="noopener noreferrer" class="share-icon twitter" title="Share on Twitter">
</a>
<a href="https://media.mailhop.org/dmarcreport/images/2024/11/What-is-DMARC-compliance-and-how-can-you-achieve-it.mp3" target="blank" rel="noopener noreferrer" class="share-icon download" title="Download" download>
</a>
Link
<input value="https://dmarcreport.com/blog/podcast/what-is-dmarc-compliance-and-how-can-you-achieve-it/" class="input-link input-link-17923" title="Episode URL" readonly />
<button class="copy-link copy-link-17923" title="Copy Episode URL" aria-label="Copy Episode URL" readonly=""></button>
Embed
/*! This file is auto-generated */ ’ title=“Embed Code” class=“input-embed input-embed-17923” readonly/>
<button class="copy-embed copy-embed-17923" title="Copy Embed Code" aria-label="Copy Embed Code"></button>
If your organization sends out marketing or bulk emails, you must make sure they reach your audience safely. While this might not seem like a big goal, it is certainly not easy to check all the boxes, given that cybercriminals are only getting better with their tactics. They are perpetually on the lookout for new targets and ways to exploit vulnerabilities, especially through email channels.
We hate to break it to you, but with phishing, ransomware, spoofing, and other grave cyberattacks on the rise, your business’s reputation and bottom line are at stake. So, when it comes to protecting your organization, you need a robust and reliable technique that will ensure that your outgoing emails securely reach their destination - the recipients’ inboxes. To make it happen, you need to implement DMARC (Domain-based Message Authentication, Reporting, and Conformance) in your email ecosystem.
DMARC is one of the most crucial email authentication protocols that protect your domain from unauthorized use by cybercriminals trying to impersonate your brand**. It builds on two other protocols - SPF and DKIM that validate whether or not emails claiming to come from your domain were actually sent by authorized parties.
As simple as it sounds, achieving DMARC compliance is not something you can achieve overnight; it requires careful **planning and ongoing monitoring to tackle evolving cyber threats.
Here is how your organization can secure its email channels and reach DMARC compliance to effectively **protect your clients and your brand reputation.

What is DMARC compliance?
Before we get into the ‘how,’ let us take you through the basics and help you understand what DMARC compliance actually means.
DMARC compliance is a security measure that helps prevent threat actors from phishing or spoofing your organization’s domains or subdomains to send out malicious emails on your part. It assures the receiving servers that all incoming emails supposedly sent from your domain have undergone two other critical protocols, which include SPF and DKIM. These two protocols work together to validate the sender of the message and whether or not it has been altered in transit. If a message fails these checks, the DMARC policy determines the course of action - the message that will be either sent to the spam folder or blocked dead in its tracks (bounce-back).
In other words, DMARC compliance translates into creating a **secure email channel that is trust-oriented and helps protect the brand and recipients from cyberattacks.
Why should your email-sending domains be DMARC-compliant?
By now, you know that DMARC implementation and compliance are absolutely necessary for organizations that send bulk emails every day, but have you ever wondered why email service providers (ESPs) like Google and Yahoo stress so much on DMARC?
Let us find out why:
Enhancing trust and security
There’s no denying that email is one of the most common and vulnerable threat vectors out there. This opens your domain to exploitation in case an attacker wants to scam your customers or partners. This is where DMARC steps in and verifies the **authenticity of emails claiming to come from your domain and blocks the email from impersonating you while sending only those messages whose senders are authorized by you.
Enhancing email deliverability
If your **email-sending domains are DMARC compliant, the ESPs are more likely to deliver your messages directly to the recipient’s inbox. It gives them the confidence that the emails are from a reliable source, are not tampered with, or contain any malicious content. Once the message reaches the client’s inbox, they will also get the assurance that the email is legitimate and safe to open. In that case, they are more likely to engage with the email, boosting your open rates and overall email campaign performance.
Offers insights and control over email activity
DMARC reports show you how your domain is being used, which you can use to find unauthorized and suspicious activity. With this information, you are better equipped to proactively manage and secure your **best practices in regard to the sending of e-mail, so much easier to adjust before it presents a problem for your organization.
Meeting industry standards for email security
One of the many advantages of DMARC compliance is, without a doubt, email security; however, if you do not follow industry standards, you expose your organization to regulatory penalties. To improve your overall cybersecurity posture and avoid legal complexities that might come up due to non-compliance, it is important to incorporate DMARC into your email security strategy.
What are the prerequisites for DMARC compliance?
To make your domains DMARC compliant and ensure only authenticated emails reach recipients’ inboxes, you need to meet a few key requirements.
Here’s what you need to have in place:
DMARC policy published in the DNS
The first step to DMARC compliance is publishing a DMARC policy for your domain in DNS. The policy is a directive to email servers on how to respond when a mail from your domain fails the DMARC check. For starters, consider the monitoring-only mode, that is, ‘p=none,’ and then move on to more stringent policies like ‘p=quarantine’ or ‘p=reject.’ The ‘p=none’ policy gives you full visibility into your email activity without affecting delivery. That makes it easy to see who is using your domain and spot any potential problems.
How Do You Configure SPF and DKIM?
In order to be compliant with DMARC, your email should pass either SPF or DKIM checks .
SPF
Sender Policy Framework or SPF checks the IP address of the email’s sending server. It ensures that your **email’s sending IP address **has been authorized and aligns with the domain in the ‘From’ address of the email.
DKIM
DKIM adds a digital signature to your emails. To verify the legitimacy of the email message, the signature should be consistent with your domain in the ‘From’ address.
PTR records
Every IP that sends emails on behalf of your domain must have a PTR record, commonly known as a reverse DNS record. This proves that the IP actually belongs to your domain and adds another **layer of credibility to your emails.
Regular monitoring
Monitoring helps to ensure you’re on track with DMARC compliance. To know the ins and outs of your email communications (in the context of security and authentication), you can rely on tools that help you track email performance, identify potential compliance issues, and also facilitate the setting up of DMARC policies.
Proper email formatting
When it comes to DMARC compliance, email formatting does matter. So, ensure that your emails adhere to the email formatting standards, such as RFC 5322.
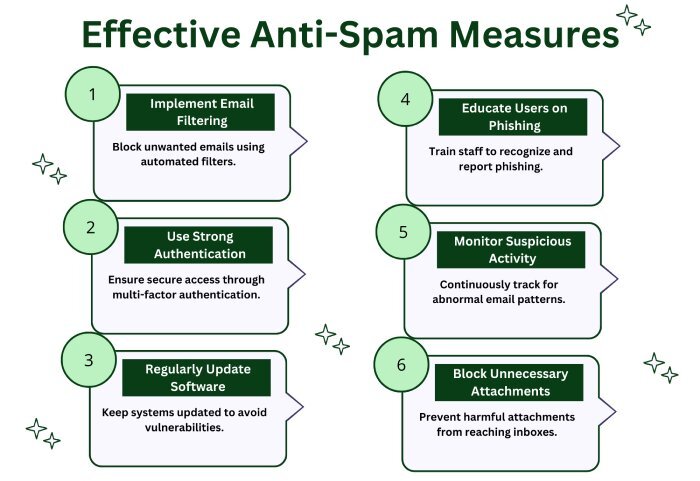
Employ anti-spam measures
Meeting anti-spam guidelines keeps your emails credible and helps achieve better deliverability. While you’re at it, make sure that your recipients have opted in to receive your messages; you should maintain low spam complaint rates, and you must also ensure that there’s an easy one-click unsubscribe option available for your audience.
How to make your email DMARC compliant?
To make your email DMARC-compliant, you’ll need to follow a few essential steps to set up the necessary protocols and monitor your domain’s email activity. Here’s how you can do it:
Start by creating an SPF or DKIM record
Start by setting up an SPF record, a DKIM record, or ideally both in your domain’s DNS settings. These records are vital for verifying that the emails coming from your domain are from authorized sources. Moreover, both records work to establish a reliable identity for your domain, which is key to achieving DMARC compliance.
Create DMARC record
Moving on, once you are done with configuring SPF and DKIM records , it’s time to create a DMARC record in your DNS. This record tells the receiving mail server what to do with those emails that do not pass authentication checks. You do this by enforcing a suitable policy.
Set a DMARC policy
Once you’ve created your DMARC record, set your policy to determine how to handle emails that don’t get through authentication checks. You can start with ‘p=none’ as it allows you to gain insights into your email traffic without taking any action against suspicious emails. Then, as you become confident with authentication, you can move on to ‘p=quarantine’ to send unauthenticated emails to spam and finally to ‘p=reject’ to block them altogether. This gradual process protects your domain and ensures legitimate email delivery.
Publish the DMARC record
After you’ve decided upon the DMARC policy and implemented it, all you’re left to do is publish the DMARC that you created in the DNS. That’s all, and your outgoing emails will now be DMARC compliant!
As established earlier, **achieving DMARC compliance is not a one-off task. An important aspect of this endeavor is DMARC reporting. It tells you about your domain’s email activity, helps you monitor authentication results, and spots any unauthorized attempts to misuse your domain.If you want your domains to be well-protected against email-based threats, our team at **DMARCReport is here to support you! To get started, book a demo with us!
Topics

Content Specialist
Content Specialist at DMARC Report. Writes vendor-specific email authentication guides and troubleshooting walkthroughs.
LinkedIn Profile →Take control of your DMARC reports
Turn raw XML into actionable dashboards. Start free - no credit card required.