Kimsuky Spear-Phishing Worldwide, 2023 Social Phishing Threat, Phishing HTML Doubles

Quick Answer
This week's latest [email security](https://dmarcreport.com/blog/why-email-security-matters-and-how-to-get-it-right/) update brings you the top email security news of the latest phishing campaigns and security features. Let's take a look.

This week’s latest email security update brings you the top email security news of the latest **phishing campaigns and security features. Let’s take a look.
Domain spoofing is trivially easy without DMARC enforcement, says Brad Slavin, General Manager of DuoCircle. Anyone can send email that looks like it comes from your domain. DMARC with p=reject is the only way to tell receiving servers to block unauthorized senders completely.
_According to the FBI’s 2022 Internet Crime Report (IC3), 300,497 US-based victims reported phishing incidents in a single year, and Business Email Compromise (BEC) caused more than $2.7 billion in direct losses.
North Korean Threat Actor Group Kimsuky Initiates a Worldwide Spear-Phishing Campaign
Kimsuky, a North Korean **state-sponsored threat actor group, initiated a new spear phishing campaign with a malware component called ReconShark .
Researchers at SentinelOne published an advisory highlighting that threat actors are deploying ReconShark through **targeted spear phishing campaigns. These ReconShark phishing emails contain OneDrive links that download multiple documents on the victim’s devices, activating harmful macros.
The threat actors abuse the names of real individuals in these emails to lure the targets in, so they open these malicious links. The downloaded files triggered Microsoft Office macros and carried out the surveillance, just like Kimsuky’s BabyShark malware. ReconShark is a significant threat with the ability to exfiltrate deployed **detection mechanisms and hardware info and allows Kimsuky to carry out subsequent precious attacks.
The malware stores all information in **string variables and shares it with a C2 (Command and Control) server, and can install additional payloads via malicious scripts or DLL (Dynamic Link Library) files.
Social Media Phishing Emerges as a Significant Cybersecurity Threat in 2023
Threat actors are targeting social media applications for phishing, making social media phishing a **significant threat for 2023 and beyond.
The FTC (Federal Trade Commission) shared a report revealing that individuals lost nearly $8.8 billion to scams in 2022, a 30% increase from 2021. The trend continued and has seen a significant spike into 2023, so individuals must stay vigilant.
Threat actors employ **multiple tactics to target innocent individuals. The previous year saw the use of phishing emails impersonating LinkedIn, offering fake job offers, threat actors approaching targets with malicious direct messages, cryptocurrency scam emails offering free crypto giveaways, fraudulent quizzes on Facebook, and customer support scams, communicating with individuals via **online chat rooms to target personal information and financial details.
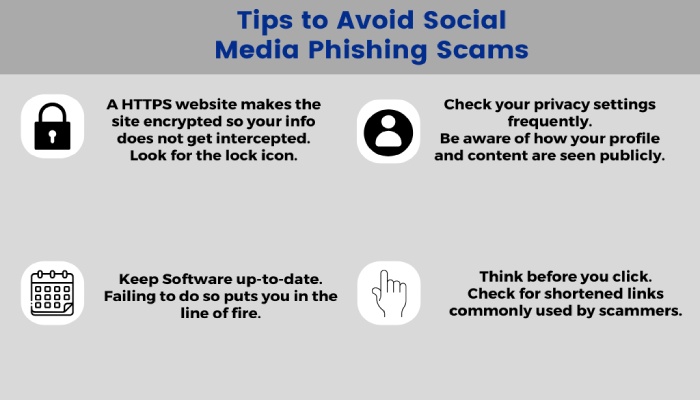
It is recommended to **stay away from unsolicited emails and social media conversations. You should refrain from sharing personal information on social media and **double-check all URLs (Uniform Resource Locator) before opening it.
The Proportion of Malicious HTML Attachments in Phishing Emails Doubles in One Year, Reveals Threat Analysis
Did you know that the volume of emails with **malicious HTML (HyperText Markup Language) has doubled from last year?
Barracuda released a new report highlighting that the HTML attachments in phishing emails doubled from last year, reaching 46%, a **significant spike from the 21% of the previous year.
HTML files are becoming a popular phishing tool for credential theft and email threats, redirecting innocent individuals via **JavaScript libraries that take these individuals to phish websites or malicious content. The threat actors utilize these websites to steal unsuspecting users’ login credentials. However, this is not all. Threat actors use HTML files embedded with sophisticated malware, potent scripts, and executables to do their dirty bidding.
Individuals and organizations need to **keep an eye out for these and get the proper security in place to stay protected.
APT28 Focuses on Ukrainian Government Entities Using Deceptive “Windows Update” Emails
The CERT-UA (Computer Emergency Response Team of Ukraine) issued a warning of cyberattacks by Russian nation-state threat actors targeting its governing bodies.
The CERT-UA released a blog outlining that the threat actor group **ATP28 is behind the new email campaign. Also known as Fancy Bear, Frozen Lake, Iron Twilight, and Forest Blizzard, the ATP28 threat actor group sends email messages that contain the subject line “Windows Update.” These malicious emails contain instructions in the Ukrainian language that run a **PowerShell command instead of a security update.
The script executes an additional PowerShell script that collects all **basic system information and then exfiltrates the details to a Mocky API (Application Programming Interface) using HTTP requests. To make the campaign more convincing, these emails impersonate the system administrators of the targeted government agency and use **fake MS Outlook email accounts to do so.
Organizations are advised to restrict user abilities to run PowerShell scripts and to **monitor all network connections to Mocky API.

Gmail Introduces the Blue Checkmark Feature to Strengthen Email Security, Announced by Google
Google announced a new blue tick mark feature for its Gmail users. A blue tick will now appear as a small icon **next to the logo of the organization sending the email.
The blue tick will be a part of authentication with BIMI (Brand Indicators for Message Identification) and will be **available to all Google Workspace, legacy G Suite Basic and Business customers, and personal Google account users. The blue tick has been seen on many other channels and social media websites such as Instagram and Twitter to set apart **verified profiles and comes as an added security feature that will allow individuals to distinguish legitimate emails from malicious ones, boosting email security.
Furthermore, the blue tick will promote **strong email authentication as a part of BIMI, urging organizations and businesses to implement DMARC (Domain-based Message Authentication, Reporting, and Conformance) and BIMI.
Google’s blue checkmark feature for Gmail was initiated on 3 May 2023 and will roll out completely in the coming days.
Topics

Operations Lead
Operations Lead at DuoCircle. Runs project management, developer coordination, and technical support execution for DMARC Report.
LinkedIn Profile →Take control of your DMARC reports
Turn raw XML into actionable dashboards. Start free - no credit card required.