SMTP Smuggling is Allowing Email Spoofing; DMARC Prevents Such Attacks

Quick Answer
In 2022, America’s Cybersecurity & Infrastructure Security Agency assessed federal and critical infrastructure partners, which revealed that [84% of employees took the bait](https://www.cisa.gov/sites/default/files/2023-02/phishing-infographic-508c.pdf) by either replying with [sensitive information](https://cybersecuritynews.com/hackers-using-malicious-javascript/) or engaging with the malicious links embedded in a spoofed email.
Related: Free DMARC Checker ·How to Create an SPF Record ·SPF Record Format

Try Our Free DMARC Checker
Validate your DMARC policy, check alignment settings, and verify reporting configuration.
Check DMARC Record →In 2022, America’s Cybersecurity & Infrastructure Security Agency assessed federal and critical infrastructure partners, which revealed that 84% of employees took the bait by either replying with sensitive information or engaging with the malicious links embedded in a spoofed email.
Domain spoofing is trivially easy without DMARC enforcement, says Brad Slavin, General Manager of DuoCircle. Anyone can send email that looks like it comes from your domain. DMARC with p=reject is the only way to tell receiving servers to block unauthorized senders completely.
_According to the FBI’s 2022 Internet Crime Report (IC3), 300,497 US-based victims reported phishing incidents in a single year, and Business Email Compromise (BEC) caused more than $2.7 billion in direct losses. What do studies and assessments like these convey?
Well, they convey that it’s easier for hackers to fool people into **sharing sensitive details or downloading malware-embedded files with techniques like social engineering, DDoS attacks, SMTP smuggling, etc.
This guide shares how SMTP smuggling is emerging as a new cyber threat and how to shield your email infrastructure from it.
What is SMTP and How it Works?
SMTP is short for Simple Mail Transfer Protocol, which **transmits email between computers and defines rules for exchanging messages between email servers. An SMTP connection is put into place to relay a message from an email client to transmit the actual content of the email.
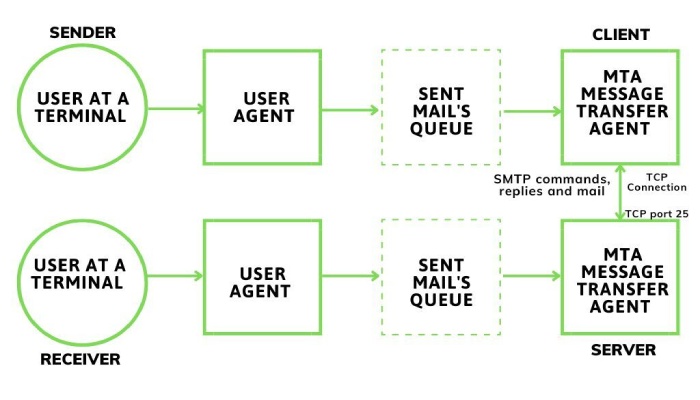
It is part of the application layer of the Internet protocol (IP) suite and works in conjunction with other protocols like POP3 (Post Office Protocol) and IMAP (Internet Message Access Protocol) that are used for email retrieval.
When you send an email, your **email client communicates with your email provider’s server using SMTP. Then, the recipient’s email server receives the email and stores it until the recipient retrieves it. SMTP is used to transmit the email message from the sender’s server to the recipient’s server. It involves a series of commands and responses between the two servers to ensure the proper handling of the email. Once the email reaches the recipient’s server, the recipient can retrieve it using protocols like POP3 or IMAP.
What is SMTP Smuggling and How is it Allowing Email Spoofing?
SMTP smuggling is a cybercrime technique used by hackers to **exploit vulnerabilities in the way email servers interpret and handle SMTP traffic. Lately, bad actors have been sending spoofed emails with fake sender addresses while bypassing security filters. Basically, they exploit the inconsistencies emerging from mishandling outbound and inbound SMTP, allowing them to smuggle arbitrary SMTP commands.
The concept of SMTP smuggling is believed to be derived from HTTPS smuggling, which misuses inconsistencies in the interpretation and processing of the Content-Length and Transfer-Encoding **HTTP headers to add an unclear or ambiguous request at the beginning of the incoming request chain.
In easier words, malicious actors tell one server that an email ends at point A and another server that it ends at point B. This **discrepancy creates a compartment in which they smuggle more data.
Other common techniques used by hackers to create inconsistencies for SMTP smuggling are:
-
Dot-stuffing (Escaping the single dot with another dot):
.. -
Replacing it with a
-
Encoding it (e.g., via quoted-printable): =0A.=0A
-
Removing the entire sequence - Not sending the message
-
Or do nothing at all
Rectification Updates
GMX Mail is believed to be the first victim of SMTP smuggling as its **outbound SMTP server allowed emails with
However, researchers have raised concerns over the Cisco Secure Email product as its vulnerabilities allow hackers to send spoofed emails to high-value targets, including Amazon, PayPal, eBay, and the IRS. Researchers advise organizations utilizing Cisco Secure Email Gateway (on-premises) or Cisco Secure Email Cloud Gateway (cloud) to modify the default settings of “CR and LF Handling” from “Clean” to “Allow.” This recommendation aligns with Cisco guidelines, providing administrators with **clear instructions on the necessary adjustment.
How Do You Protect Your Domains With SPF, DKIM, and DMARC?
SMTP doesn’t have an authentication mechanism embedded in it, which underlines the need to have SPF, DKIM, and DMARC in place to **safeguard your domains from getting exploited for attempting phishing and email spoofing attacks.
SPF uses a TXT record to inform recipient servers which IP addresses are allowed to send emails for a given domain. Emails sent from IP addresses outside of the list are either marked as spam or bounce back, depending on the SPF mechanism chosen by the domain owner or SPF administrator.
DKIM performs **authentication checks by signing outgoing emails with a private key , and upon reception, the recipient server matches it with the public key retrieved from the domain’s DNS.
DMARC checks the alignment of the email’s “From” domain with SPF checks and/or DKIM signatures. Consequently, if there is a discrepancy between the MAIL FROM and the From domain, which would otherwise allow the SPF check to pass, the DMARC check will fail.
Wrapping it

Since forged emails look like they are sent by legitimate people, recipients end up trusting them and sharing sensitive details or transferring money. However, organizations can still mitigate the risks by educating their employees about the red flags of a phishing email and deploying email security protocols.
DMARC reporting and monitoring is one such practice that gives domain owners the power to look into their domain’s email activities to filter out unauthorized and malicious senders. We offer DMARC reporting solutions for MSPs, service providers, and businesses managing many domains for DMARC compliance. Book a demo today to understand our working style better.
Topics

Operations Lead
Operations Lead at DuoCircle. Runs project management, developer coordination, and technical support execution for DMARC Report.
LinkedIn Profile →Take control of your DMARC reports
Turn raw XML into actionable dashboards. Start free - no credit card required.